Introduction
The growing dependence on embedded systems within medical devices has elevated cybersecurity to a paramount concern for healthcare organizations globally. Alarming statistics indicate that more than 67% of healthcare institutions have experienced ransomware attacks, underscoring the heightened stakes in this arena. This article explores essential practices for bolstering cybersecurity in these systems, providing manufacturers with a strategic framework to protect patient safety and adhere to evolving regulatory standards. As threats continue to advance, manufacturers must consider how to ensure their defenses remain robust and effective against emerging vulnerabilities.
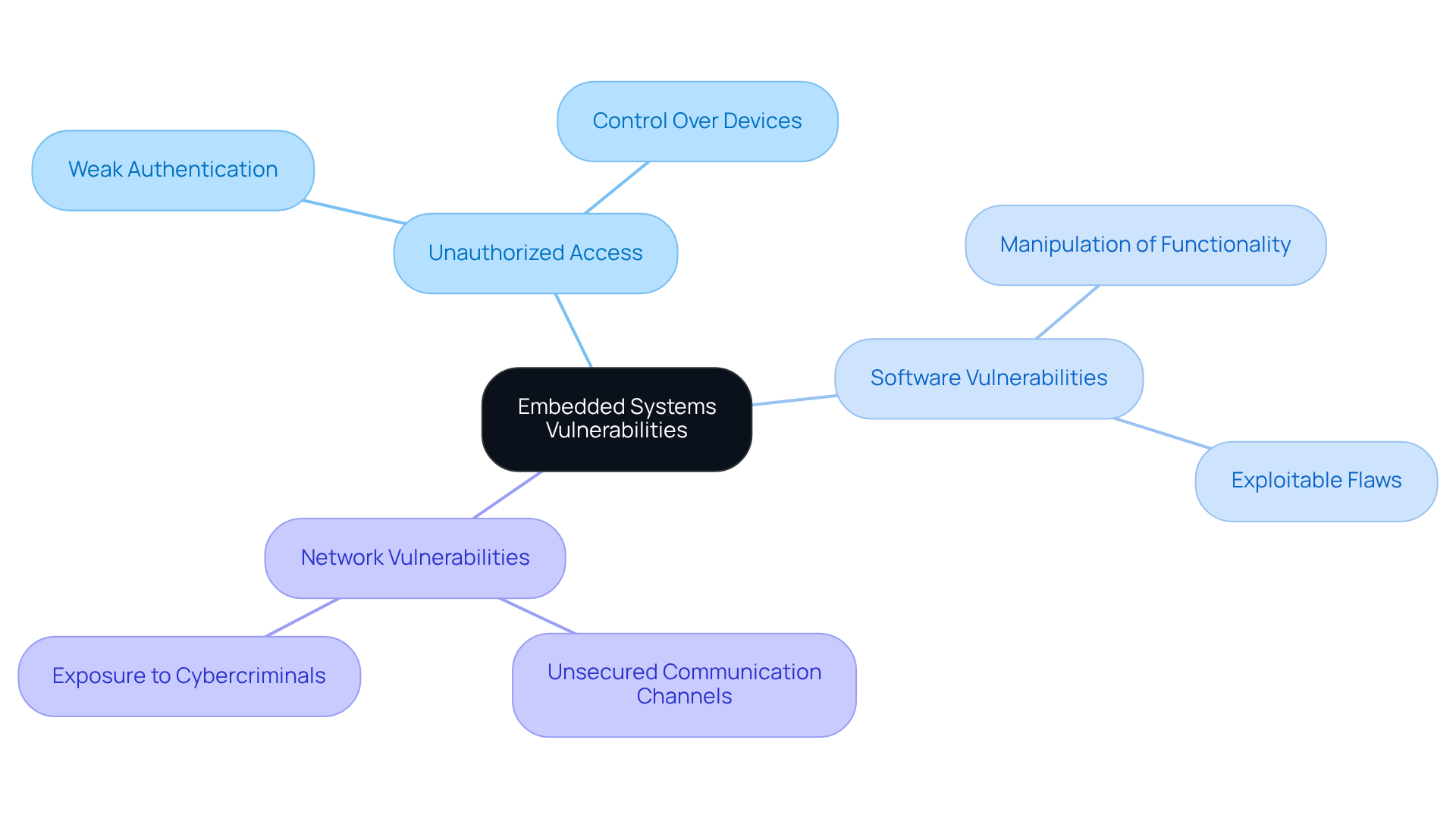
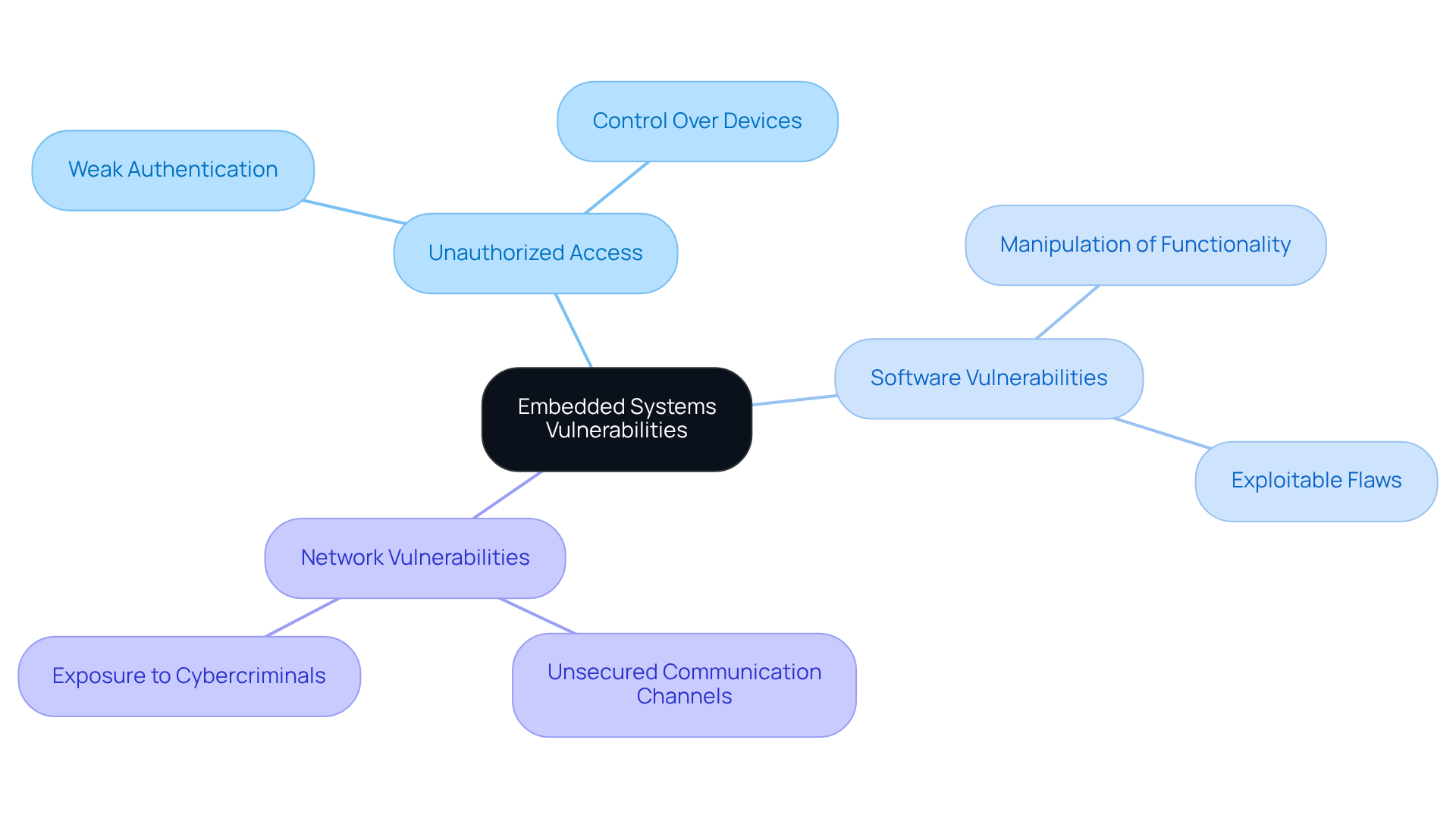
Understand Embedded Systems Vulnerabilities
Cyber security embedded systems in medical equipment face increasing susceptibility to various threats, notably unauthorized access, software vulnerabilities, and inadequate security measures. Key attack vectors include:
- Unauthorized Access: Attackers frequently exploit weak authentication mechanisms, gaining control over devices and potentially jeopardizing patient safety.
- Software Vulnerabilities: Flaws within the software can be exploited, enabling attackers to manipulate system functionality, which may lead to severe consequences in clinical settings.
- Network Vulnerabilities: Devices connected to networks are exposed through unsecured communication channels, rendering them attractive targets for cybercriminals.
In 2024, over 67% of healthcare organizations reported experiencing ransomware attacks, underscoring the urgency of addressing these vulnerabilities. Furthermore, 99% of hospitals possess at least one piece of equipment with recognized exploited vulnerabilities, illustrating the prevalence of risks in medical environments.
To effectively mitigate these vulnerabilities in cyber security embedded systems, conducting a thorough threat modeling exercise tailored to the specific architecture and functionality of each unit is essential. This proactive strategy enables the implementation of targeted security measures, thereby enhancing system integrity and ensuring patient safety.
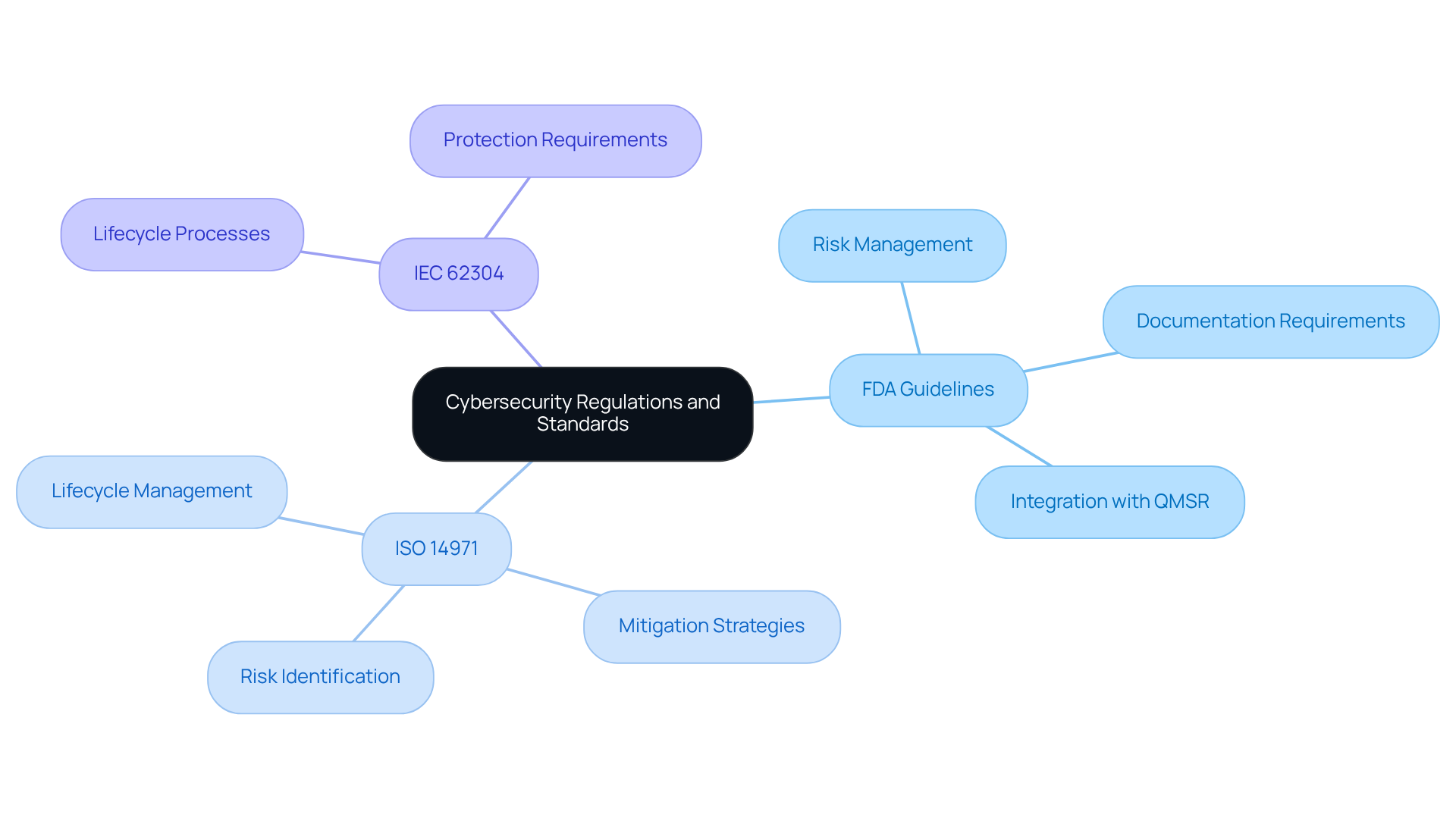
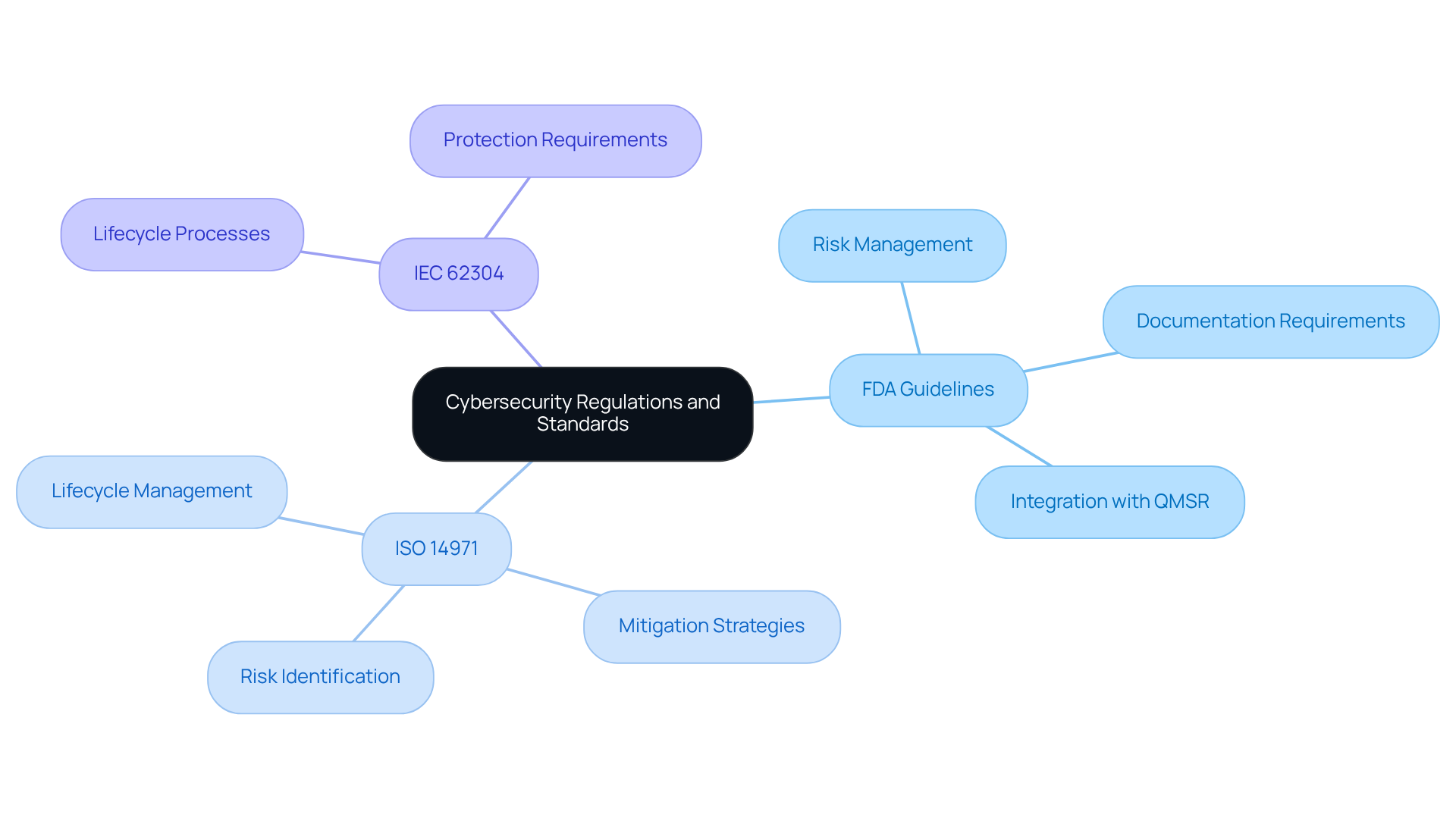
Navigate Cybersecurity Regulations and Standards
Compliance with cybersecurity regulations is essential for medical device manufacturers, guided by key standards that shape their efforts:
- FDA Guidelines: The FDA provides comprehensive guidance on cybersecurity for medical devices, emphasizing the necessity of risk management and detailed documentation in premarket submissions. This includes the integration of cyber security embedded systems into the overall quality management system, as mandated by the new Quality Management System Regulation (QMSR).
- ISO 14971: This standard plays a vital role in implementing risk management for healthcare tools, focusing on the identification and mitigation of cybersecurity challenges throughout the product lifecycle. It underscores that manufacturers must systematically address cyber security embedded systems alongside traditional safety risks, ensuring that threats are documented and managed effectively.
- IEC 62304: This standard delineates the lifecycle processes for medical equipment software, incorporating essential protection requirements that must be adhered to during both development and maintenance.
To achieve compliance, manufacturers should establish a robust strategy that encompasses regular audits, comprehensive documentation of protective measures, and strict adherence to these standards. This proactive approach not only fulfills regulatory requirements but also upholds high safety and protection standards, ultimately safeguarding patient health and the integrity of the equipment.
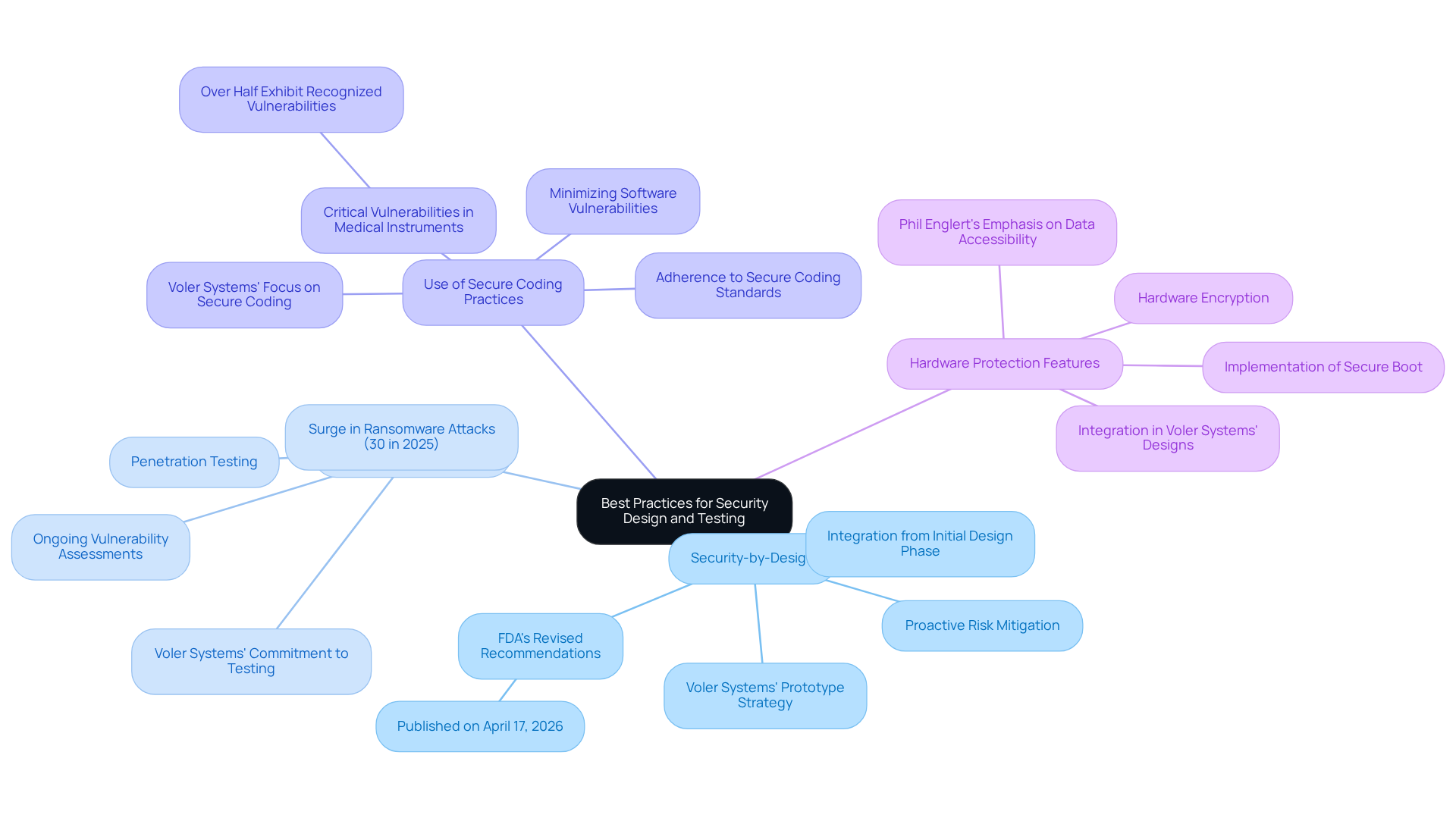
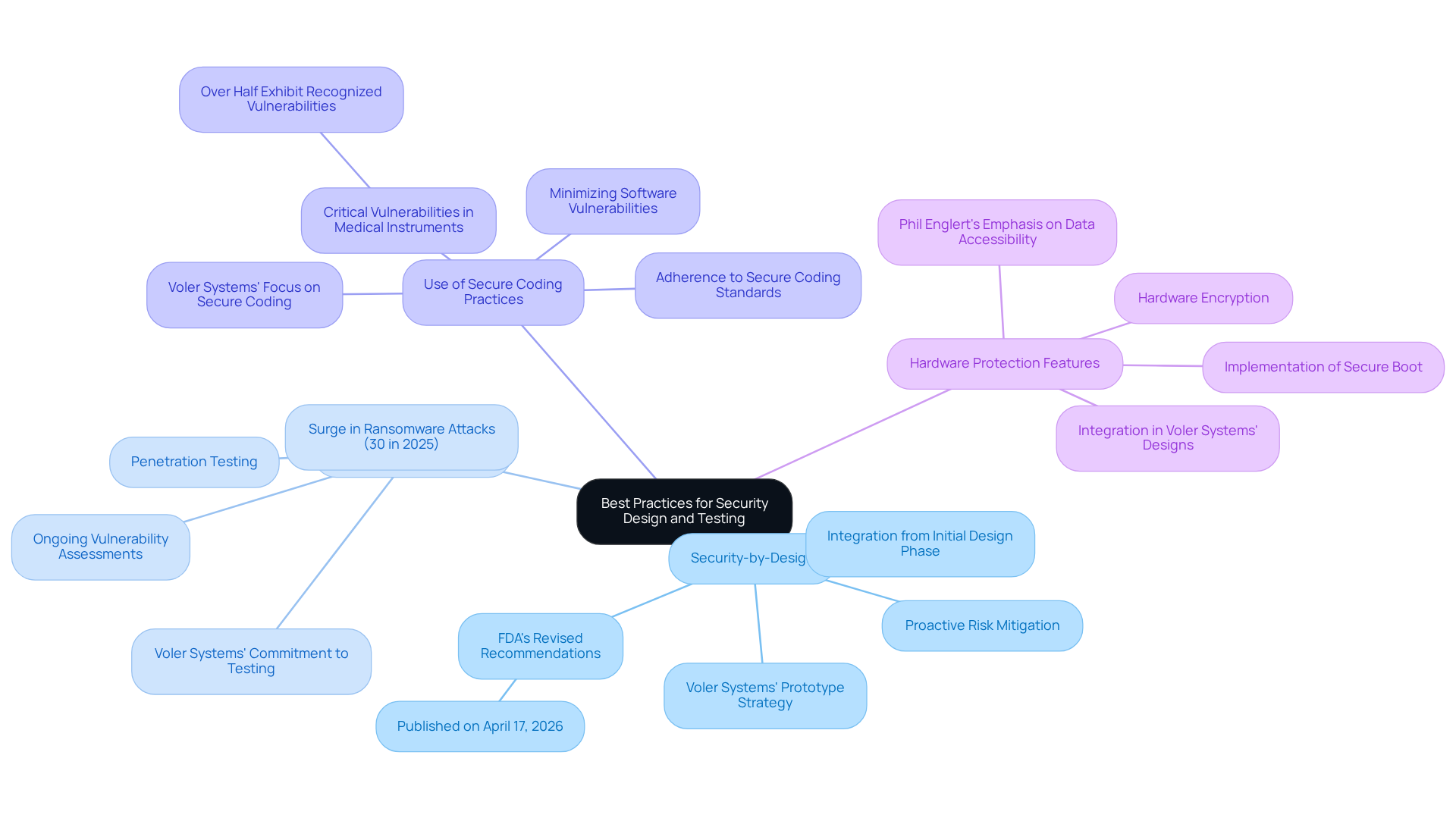
Implement Best Practices for Security Design and Testing
To enhance the security of embedded systems in medical devices, manufacturers should adopt the following practices:
- Security-by-Design: Security features must be integrated from the initial design phase, establishing security as a fundamental aspect of the device architecture. This proactive approach is crucial for mitigating risks associated with vulnerabilities. The FDA's revised recommendations on cyber security embedded systems for medical devices, published on April 17, 2026, highlight the importance of incorporating protection from the outset. Voler Systems exemplifies this approach through its prototype strategy, which streamlines hardware development while ensuring that considerations for cyber security embedded systems are woven into the design process.
- Regular Security Testing: Ongoing vulnerability assessments and penetration testing should be conducted throughout the development lifecycle. This practice is essential for identifying and rectifying potential vulnerabilities before they can be exploited. Notably, healthcare-related ransomware attacks surged by 30% in 2025, highlighting the critical need for regular testing. Voler Systems' commitment to rigorous testing procedures during the prototype stage effectively addresses these challenges.
- Use of Secure Coding Practices: Adhering to secure coding standards is vital for minimizing software vulnerabilities, such as buffer overflows and injection attacks. This adherence reduces the risk of exploitation and enhances overall system protection. Alarmingly, more than half of linked medical instruments in hospitals exhibit recognized critical vulnerabilities, emphasizing the necessity for stringent coding practices. Voler Systems prioritizes secure coding in its development processes, emphasizing the importance of cyber security embedded systems to ensure that software remains resilient against potential threats.
- Hardware Protection Features: Implementing hardware-based protective measures, including secure boot and hardware encryption, is essential for safeguarding sensitive data and maintaining equipment integrity. Phil Englert, Director of Medical Equipment Security at Health-ISAC, emphasizes that ensuring availability and data accessibility is crucial for effective patient care. Voler Systems integrates these hardware protection features into its designs, thereby enhancing the reliability of healthcare instruments.
These practices not only bolster the protection of equipment but also ensure compliance with evolving regulatory standards, ultimately contributing to the development of safer healthcare instruments through cyber security embedded systems. Manufacturers should be aware of common pitfalls, such as underestimating the complexity of integrating protective features or neglecting to update protective measures in legacy equipment. Real-world examples of successful implementations, including those by Voler Systems, further illustrate the effectiveness of these practices.
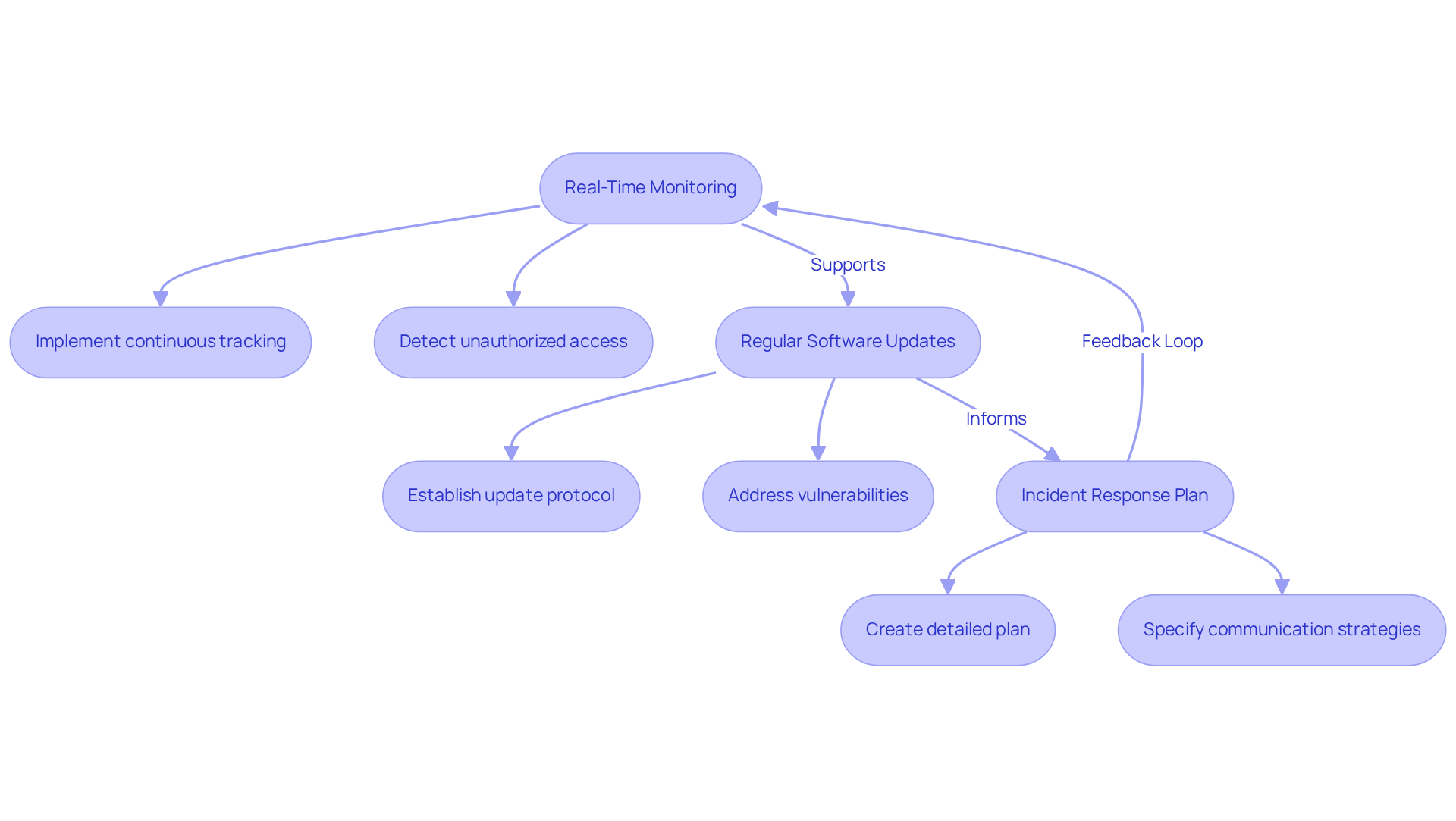
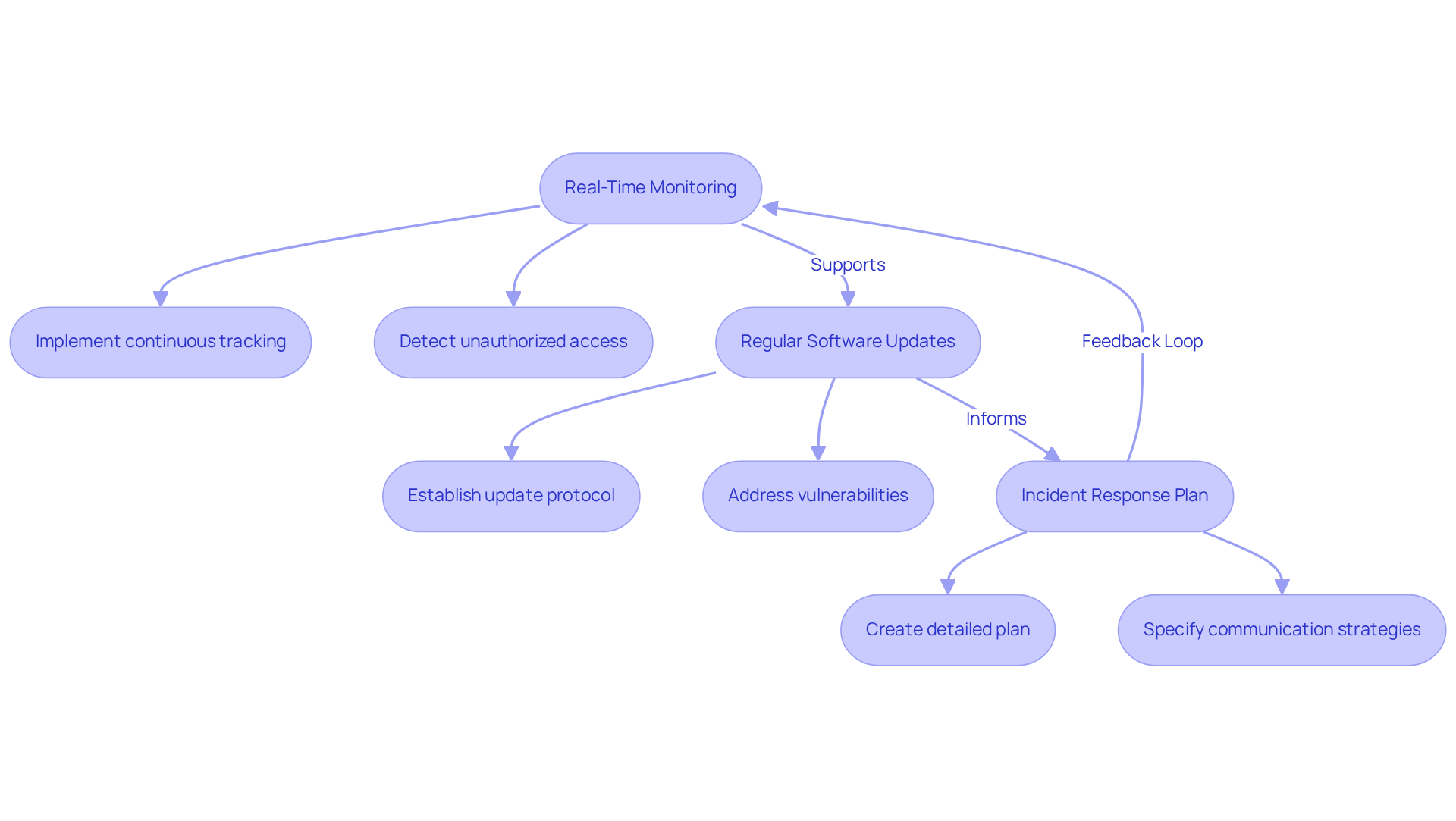
Maintain Continuous Security Monitoring and Updates
To ensure the ongoing cyber security of embedded systems in medical devices, manufacturers must prioritize continuous monitoring and regular software updates.
- Real-Time Monitoring: It is essential to implement systems that continuously track device activity and network traffic to detect unauthorized access or anomalies. This proactive approach is crucial, as incidents in cyber security embedded systems can disrupt clinical workflows and delay patient care, highlighting the need for vigilance.
- Regular Software Updates: Establishing a protocol for timely software updates and patches is vital to address newly discovered vulnerabilities. The FDA emphasizes that secure software updates are no longer optional; they are critical for maintaining patient safety and regulatory compliance. Frequent updates help mitigate risks associated with outdated equipment, which often remains in operation for years, leading to ongoing vulnerability to threats.
- Incident Response Plan: A detailed incident response plan should be created, specifying procedures for managing breaches. This plan must include communication strategies and remediation steps to ensure a swift and effective response to any cybersecurity incidents.
By adopting a proactive security strategy, manufacturers can significantly reduce the risk of cyber threats to cyber security embedded systems, thereby ensuring the long-term safety and effectiveness of their medical devices. The shift towards viewing cybersecurity as a core operational strategy reflects the growing recognition of its importance in healthcare, where patient safety is paramount.
Conclusion
Addressing the challenges of cybersecurity in embedded systems for medical devices is essential for safeguarding patient health and ensuring the integrity of healthcare technologies. This article underscores the necessity of understanding vulnerabilities, adhering to regulatory standards, implementing best practices in design and testing, and maintaining continuous security monitoring. By concentrating on these areas, manufacturers can establish a robust framework that not only mitigates risks but also enhances overall patient safety.
Key insights emphasize the importance of proactive measures such as:
- Threat modeling
- Compliance with FDA guidelines
- Integration of security features from the design phase
Regular security testing and timely software updates are critical practices that help defend against emerging threats. Furthermore, a commitment to continuous monitoring ensures that any potential breaches are swiftly addressed, minimizing the impact on clinical operations.
Given the increasing prevalence of cyber threats in healthcare, it is imperative for manufacturers to prioritize cybersecurity as a fundamental aspect of their operational strategy. By adopting these best practices, the medical device industry can not only comply with evolving regulations but also cultivate a culture of safety and resilience against cyber threats. Taking decisive action now will pave the way for a more secure future in healthcare technology, ultimately protecting both patients and providers from the risks associated with cyber vulnerabilities.
Frequently Asked Questions
What are the main vulnerabilities in embedded systems for medical equipment?
The main vulnerabilities include unauthorized access, software vulnerabilities, and inadequate security measures.
How do attackers exploit unauthorized access in medical devices?
Attackers exploit weak authentication mechanisms to gain control over devices, which can jeopardize patient safety.
What are software vulnerabilities, and how do they affect medical equipment?
Software vulnerabilities are flaws within the software that can be exploited by attackers to manipulate system functionality, potentially leading to severe consequences in clinical settings.
Why are network vulnerabilities a concern for embedded systems in healthcare?
Devices connected to networks are exposed through unsecured communication channels, making them attractive targets for cybercriminals.
What statistics highlight the urgency of addressing vulnerabilities in healthcare cyber security?
In 2024, over 67% of healthcare organizations reported experiencing ransomware attacks, and 99% of hospitals have at least one piece of equipment with recognized exploited vulnerabilities.
How can healthcare organizations mitigate vulnerabilities in embedded systems?
Organizations can mitigate vulnerabilities by conducting thorough threat modeling exercises tailored to the specific architecture and functionality of each unit, allowing for the implementation of targeted security measures.
List of Sources
- Understand Embedded Systems Vulnerabilities
- New Standards Aim to Protect Medical Patients from the ‘Internet of Things’ (https://fdd.org/analysis/2026/04/06/new-standards-aim-to-protect-medical-patients-from-the-internet-of-things)
- 7 Cybersecurity Threats Every Healthcare Provider Must Know in 2026 (And How to Stop Them) - Alis Technology (https://alistechnology.com/7-cybersecurity-threats-every-healthcare-provider-must-know-in-2026-and-how-to-stop-them)
- Medical Device Breach Statistics 2026 Report (https://ordr.net/medical-device-breach-statistics)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- Navigate Cybersecurity Regulations and Standards
- Navigating FDA’s Cybersecurity in Medical Devices Guidance (https://exponent.com/article/navigating-fdas-cybersecurity-medical-devices-guidance)
- FDA issues revised cybersecurity premarket submission guidance to align with quality management system regulation | DLA Piper (https://dlapiper.com/insights/publications/2026/02/fda-issues-revised-cybersecurity-premarket-submission-guidance)
- Navigating FDA's Updated Cybersecurity Guidance for Medical Devices (https://hcinnovationgroup.com/cybersecurity/medical-device-security/article/55371766/fdas-updated-guidance-on-cybersecurity-in-medical-devices)
- FDA Cybersecurity Guidance 2026: What Changed? (https://hattrick-it.com/blog/cybersecurityguidanceupdate)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- Implement Best Practices for Security Design and Testing
- New Standards Aim to Protect Medical Patients from the ‘Internet of Things’ (https://fdd.org/analysis/2026/04/06/new-standards-aim-to-protect-medical-patients-from-the-internet-of-things)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- Navigating FDA's Updated Cybersecurity Guidance for Medical Devices (https://hcinnovationgroup.com/cybersecurity/medical-device-security/article/55371766/fdas-updated-guidance-on-cybersecurity-in-medical-devices)
- Why many existing medical devices fall short of the FDA's new cybersecurity standards (https://todaysmedicaldevelopments.com/news/why-many-existing-medical-devices-fall-short-fda-new-cybersecurity-standards)
- FDA calls for ‘Secure-by-Design’ cybersecurity for medical devices | Fortified Health Security (https://linkedin.com/posts/fortified-health-security_fda-calls-for-secure-by-design-cybersecurity-activity-7343959988245065730-TNF_)
- Maintain Continuous Security Monitoring and Updates
- Theodore Cohen: The Importance of Software Security Updates for Medical Devices | AAMI Blog (https://array.aami.org/content/blog-post/theodore-cohen-importance-software-security-updates-medical-devices)
- Elevating Healthcare Cybersecurity Beyond Medical Devices in 2026 (https://armis.com/blog/elevating-healthcare-cybersecurity-beyond-medical-devices-in-2026)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- Ensuring Secure Software Updates for Medical Devices | Bold Type (https://boldtype.com/resources/secure-software-updates)