Introduction
In an industry where patient safety is paramount, ensuring the integrity of medical devices is a critical concern. Trusted boot technology emerges as a vital safeguard, enabling manufacturers to verify that only authorized software powers on their devices. This process protects sensitive patient data and maintains compliance with regulatory standards.
Implementing trusted boot presents significant challenges, particularly for smaller manufacturers who may struggle with key management and associated costs. What strategies can medical device companies employ to navigate these hurdles and effectively integrate trusted boot, thereby enhancing security and patient trust?
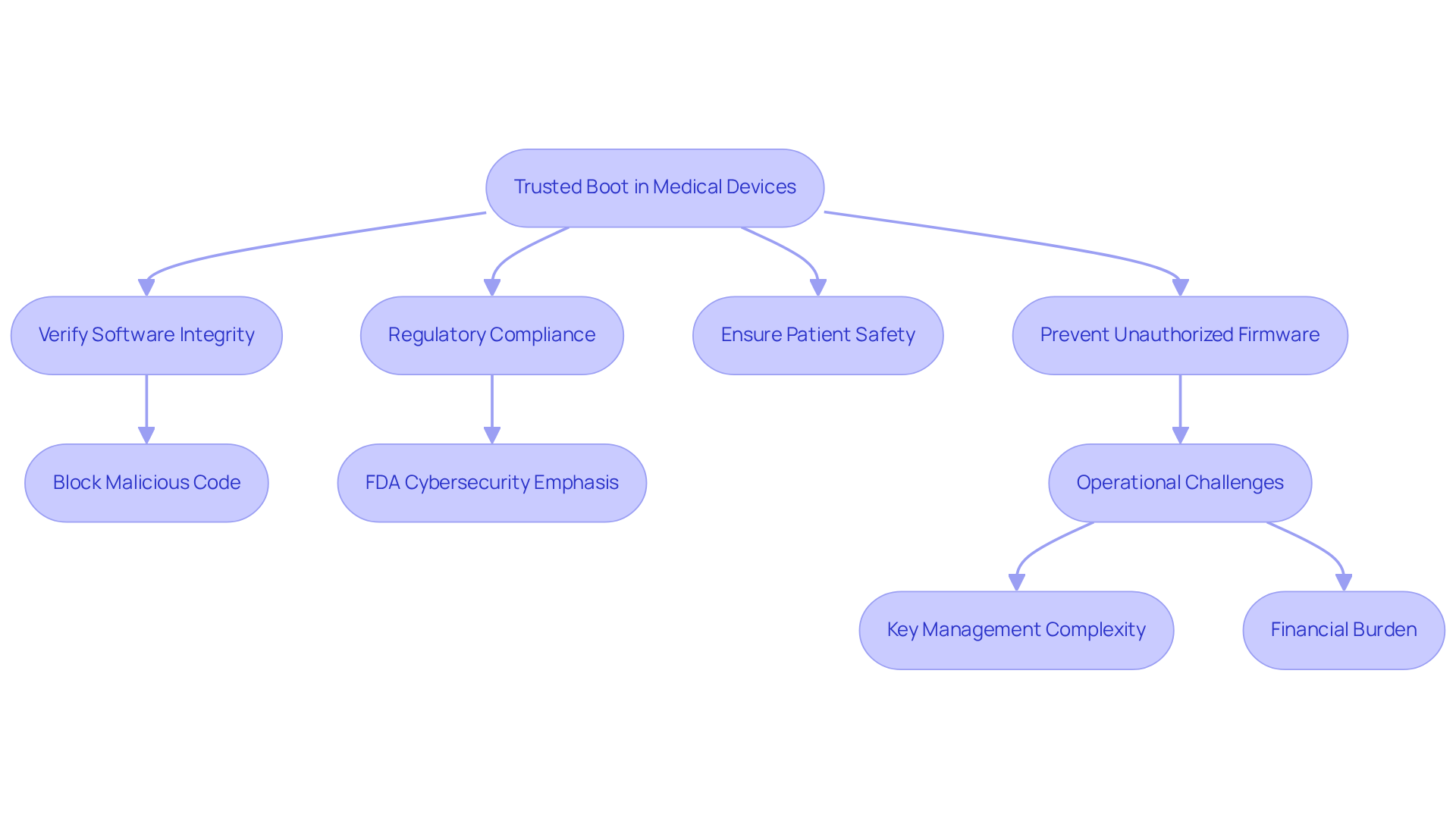
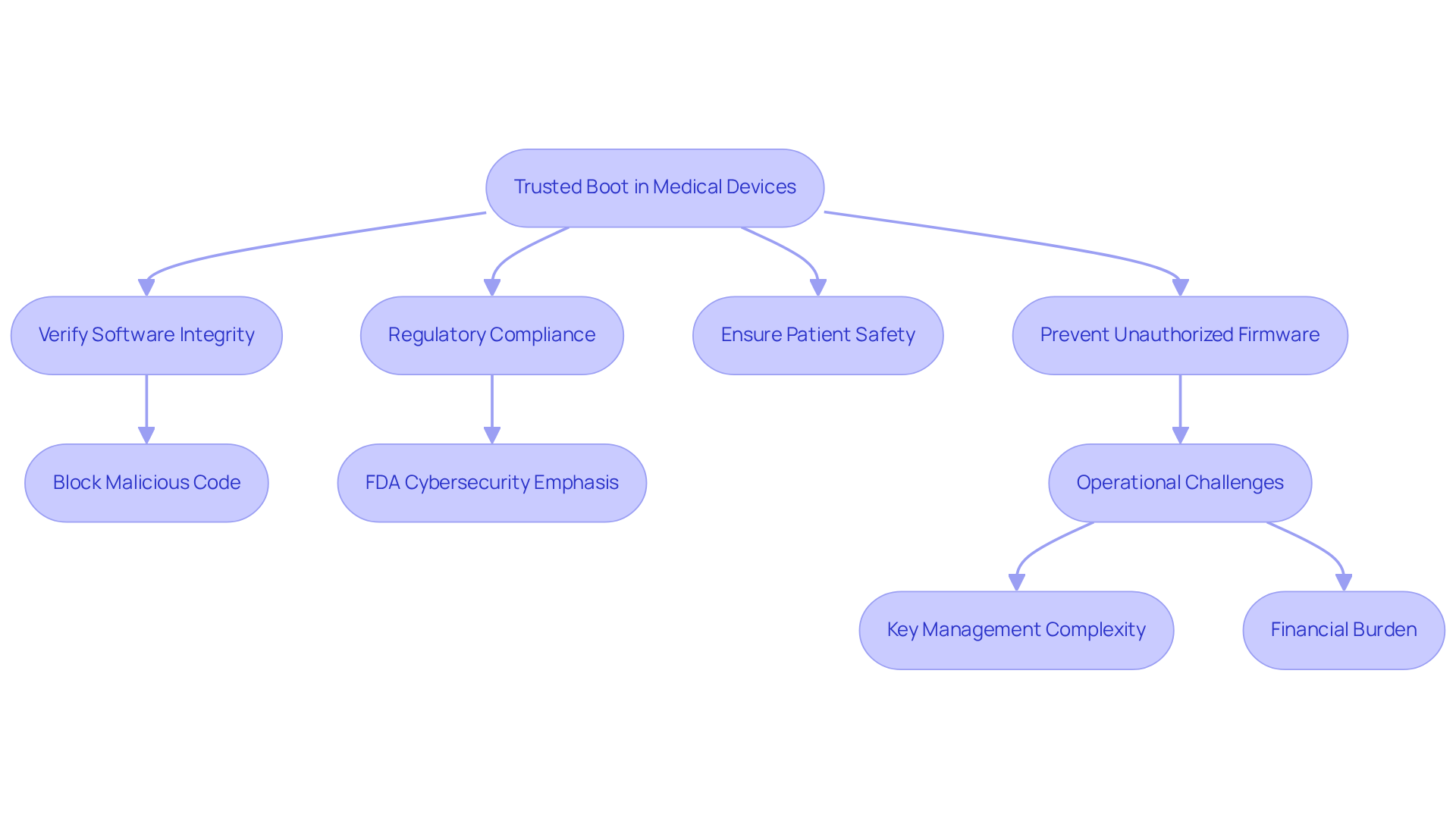
Understand the Importance of Trusted Boot in Medical Devices
In the medical device industry, ensuring that equipment powers on with verified software is critical for safeguarding patient safety. This is crucial in healthcare, where devices manage sensitive patient data and perform life-sustaining functions. Secure Startup allows manufacturers to block unauthorized firmware, preventing system malfunctions and data breaches. If a medical device fails to verify its software integrity during boot, it may run malicious code, endangering patient safety. Implementing Secure Startup serves as both a technical safeguard and a commitment to patient safety and regulatory compliance.
With the FDA emphasizing cybersecurity in medical equipment, adopting Secure Startup is vital for manufacturers to protect their products and comply with regulations. Voler Systems highlights the importance of integrating protective measures like trusted boot early in the design process, prioritizing collaboration and modifications.
Manufacturers face operational challenges in key management, especially in environments with many units, where managing cryptographic keys can be complex. The financial burden of implementing secure boot may hinder smaller manufacturers, requiring careful budgeting and resource allocation.
Sudeep Khuraijam, a security leader, states, 'Trusted boot ensures systems start with software that is trusted by the manufacturer.' This protection ensures that the operating software is authentic and uncompromised.
As cybersecurity spending by medical equipment firms is expected to reach $1.2 billion by 2027, the importance of Secure Startup in ensuring patient safety and regulatory compliance is paramount.
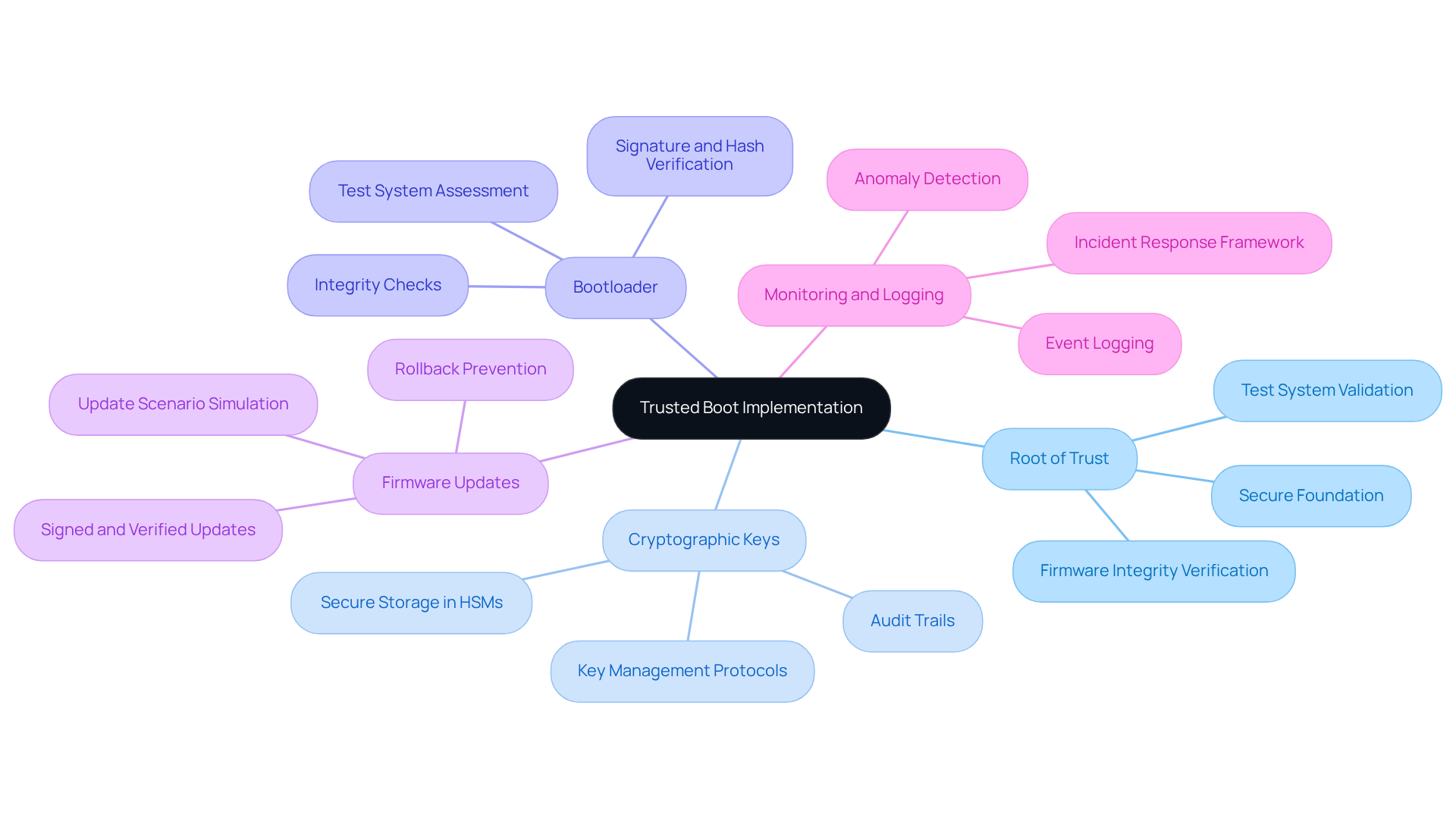
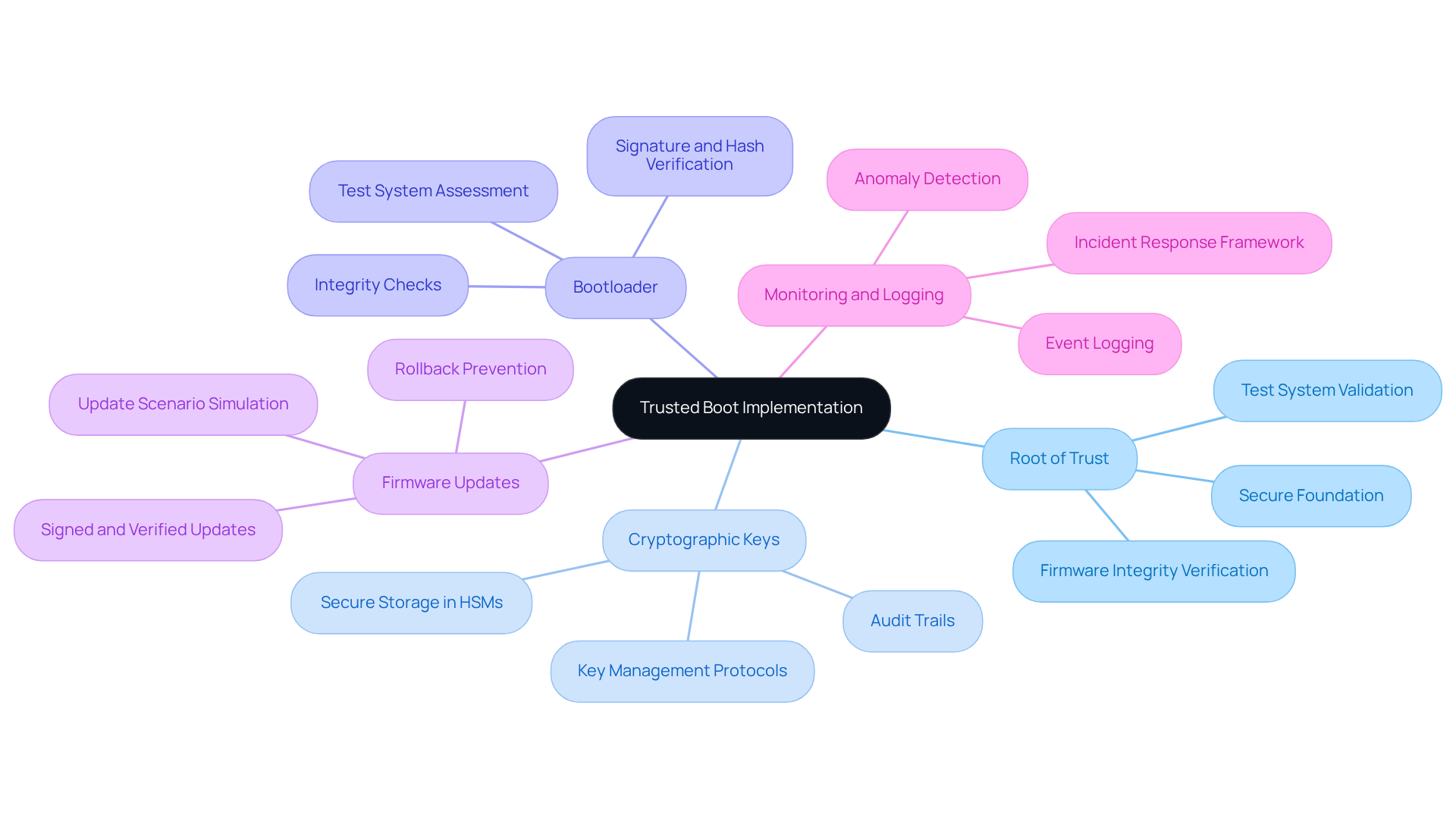
Identify Key Components for Effective Trusted Boot Implementation
To effectively implement Trusted Boot in medical devices, it is crucial to integrate several key components into the device architecture:
- Root of Trust: This hardware-based component establishes a secure foundation for the boot process, verifying the integrity of firmware before execution. A robust Root of Trust is essential for maintaining security, as it ensures that only authorized software is executed during the trusted boot sequence. Test systems validate the Root of Trust by simulating boot scenarios to confirm reliability.
- Cryptographic Keys: Secure Boot relies on cryptographic keys to sign firmware and software updates. These keys must be securely stored in certified Hardware Security Modules (HSMs) with strict audit trails to prevent unauthorized access and ensure integrity throughout the equipment lifecycle. Test systems help verify the secure storage and management of these keys through rigorous testing protocols, which are essential for a trusted boot.
- Bootloader: A secure bootloader is crucial for verifying the integrity of the operating system and applications before they are loaded. It should be designed to check signatures and hashes against known good values, ensuring that only trusted boot components are executed. Test systems assess the bootloader's effectiveness by conducting integrity checks during the boot process.
- Firmware Updates: Implementing a secure method for firmware updates is vital. This includes ensuring that updates are signed and verified before installation, which protects against the risks associated with outdated or compromised software versions. Test systems simulate update scenarios to ensure that the verification process is robust and effective.
- Monitoring and Logging: Continuous monitoring of the boot process and logging any anomalies can help identify potential security breaches early. Effective logging should capture key events, including user actions and configuration changes, to facilitate timely incident response. Test systems can simulate various attack vectors and assess the responsiveness of logging mechanisms.
By ensuring these components are integrated and utilizing test systems throughout development, manufacturers can create a secure environment that incorporates trusted boot. This safeguards against unauthorized access and maintains the integrity of medical instruments, enhancing patient safety and regulatory compliance. Neglecting these security measures could result in severe implications for patient safety and regulatory compliance.
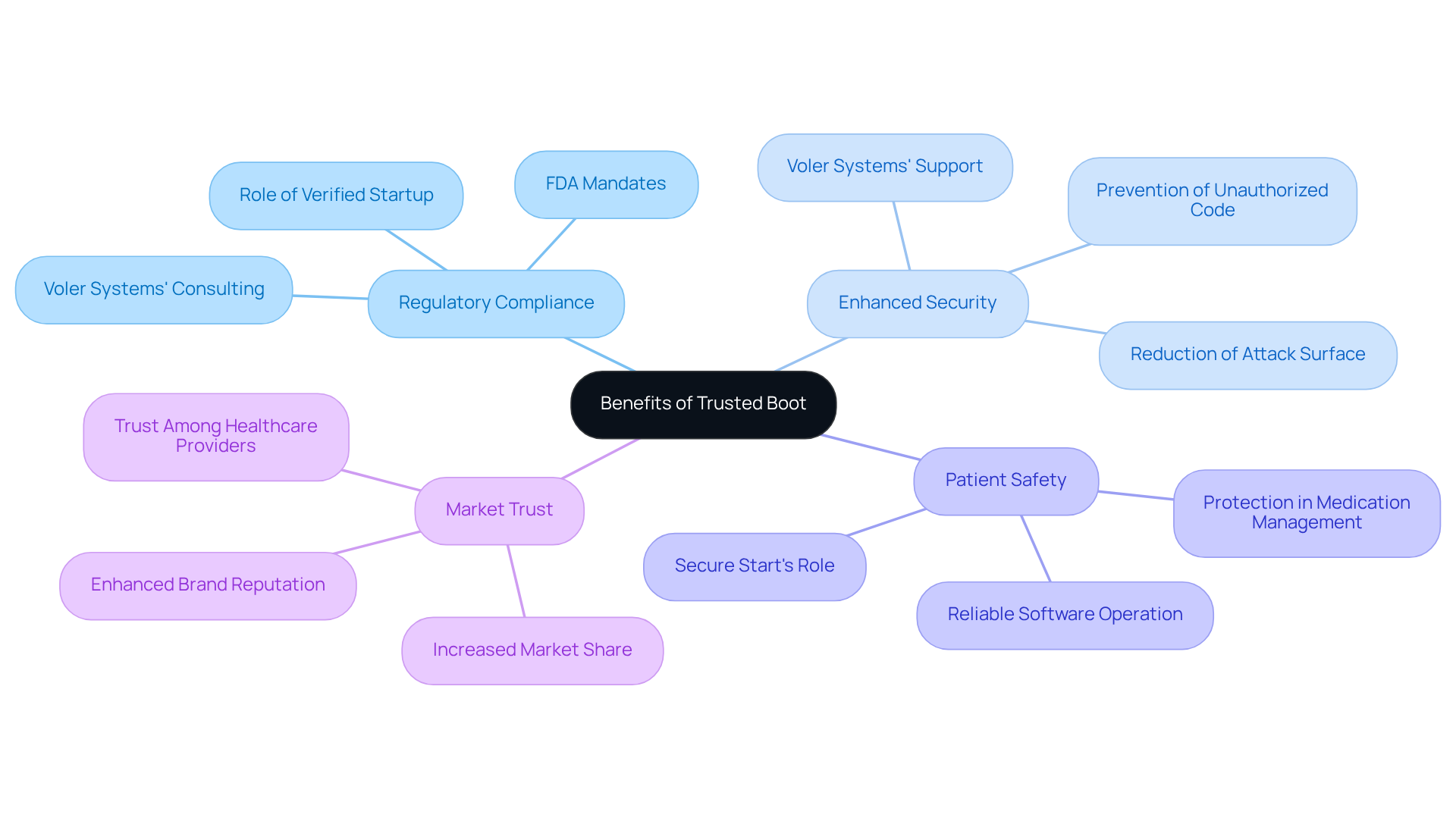
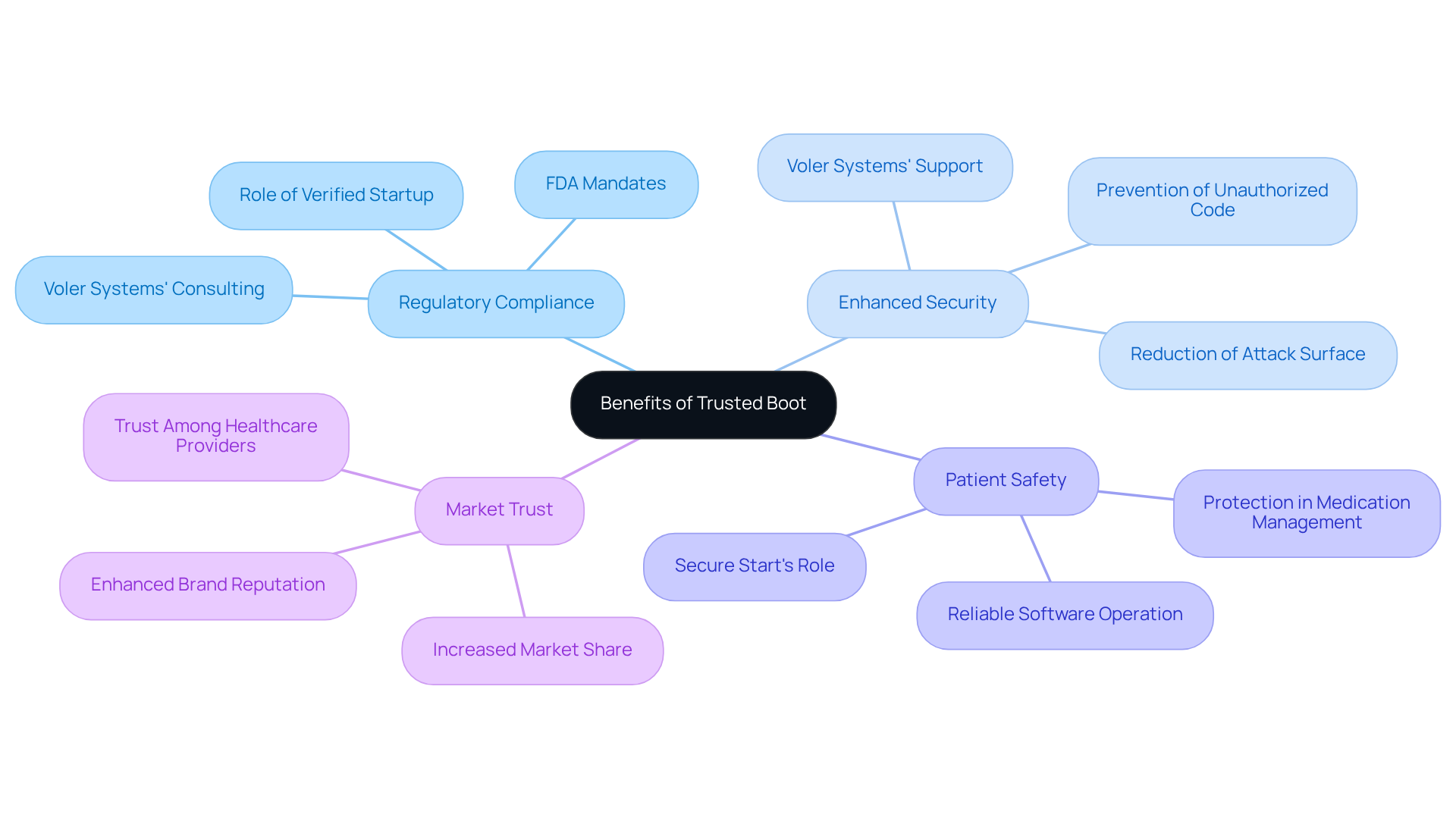
Explore Benefits of Trusted Boot for Regulatory Compliance and Security
Implementing Trusted Boot in medical devices not only addresses regulatory compliance but also significantly enhances security measures:
- Regulatory Compliance: Regulatory authorities, including the FDA, mandate that medical equipment incorporate robust security measures. Verified Startup helps producers fulfill these criteria by guaranteeing that only authenticated software runs on the system, thus reducing the chance of non-compliance. Voler Systems provides IoT consulting services that assist manufacturers in effectively navigating regulatory landscapes.
- Enhanced Security: Trusted Boot effectively reduces the attack surface by preventing unauthorized code from executing during the boot process. Without trusted boot, unauthorized code could compromise patient data and system reliability. Voler Systems provides targeted support for developing secure IoT solutions that address these critical security challenges.
- Patient Safety: By ensuring that only reliable software operates, Secure Start plays a vital role in patient safety. For example, devices that manage medication dosages must operate without the possibility of interference, a protection that Secure Startup offers.
- Market Trust: This commitment to security can lead to increased market share and customer loyalty. Incorporating trusted boot can enhance brand reputation and foster trust among healthcare providers and patients. Voler Systems' innovative approach to medical equipment design reinforces this market trust.
Ultimately, the integration of Verified Startup not only fortifies device security but also elevates the standard of care in medical technology.
Implement Trusted Boot in Existing Medical Device Designs
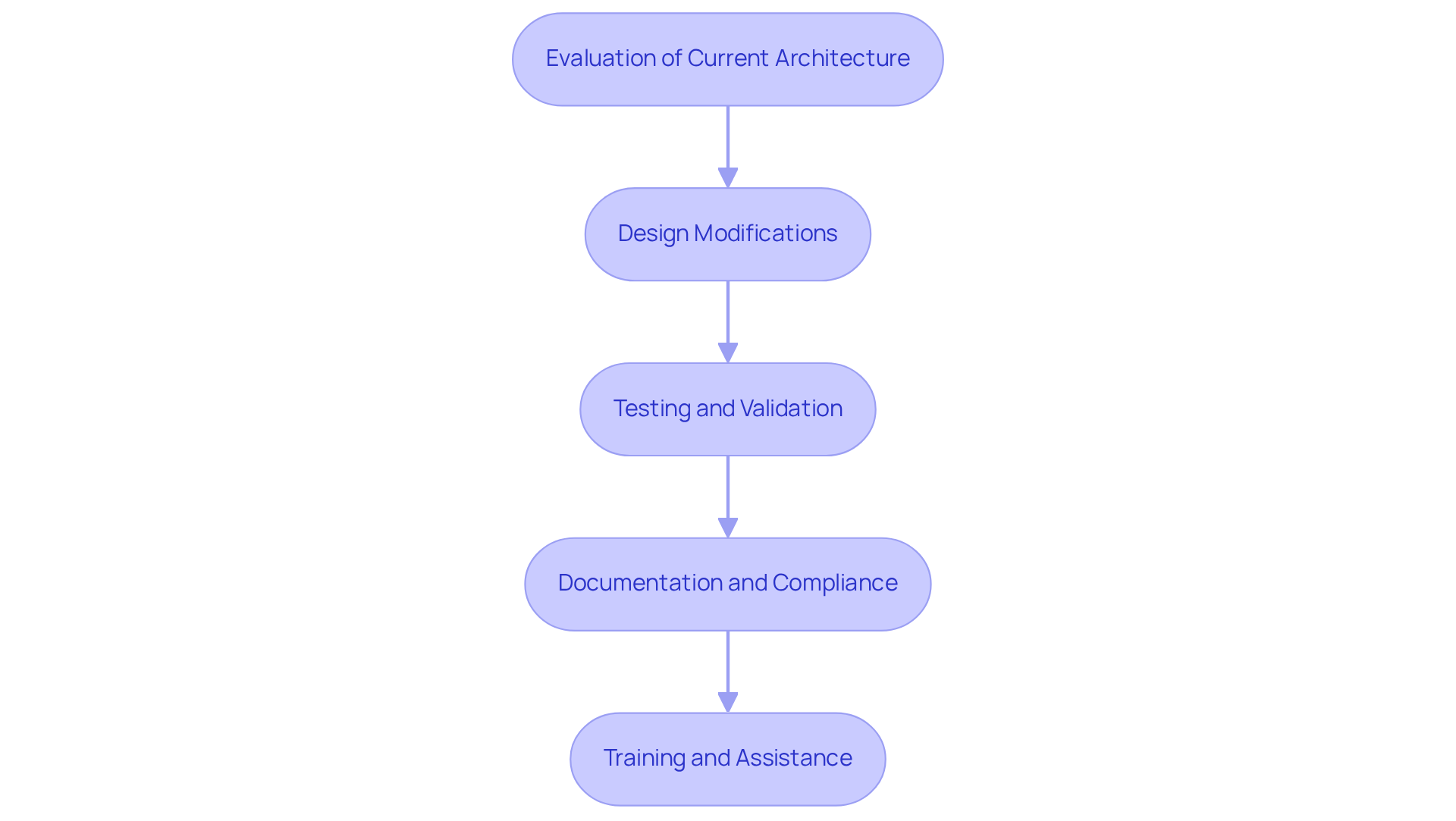
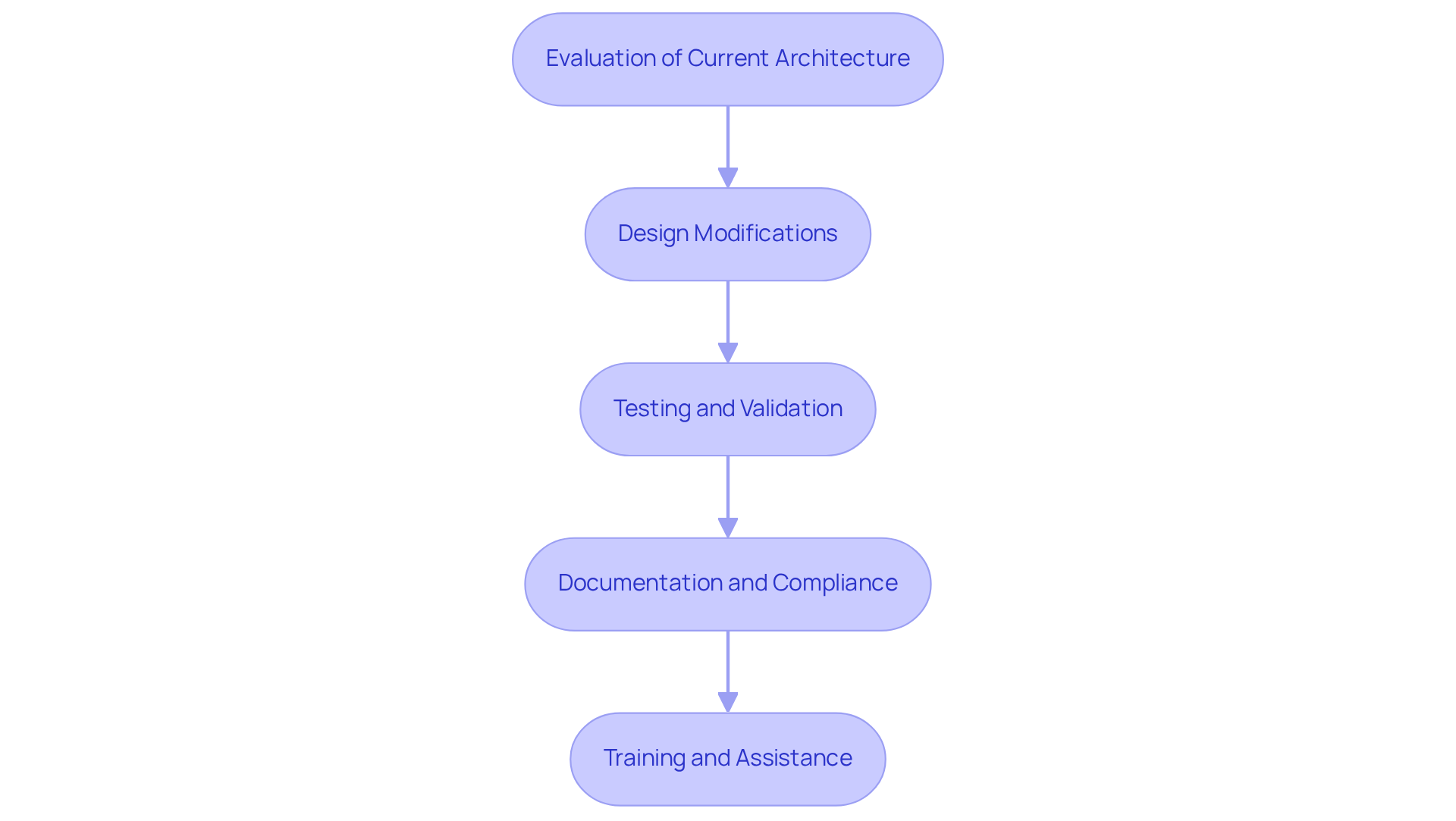
Integrating secure startup into existing medical equipment designs presents significant challenges that must be addressed to enhance security. Here are essential steps to consider:
- Evaluation of Current Architecture: Assess the current system architecture to identify opportunities for secure boot integration. This involves a comprehensive review of the bootloader, firmware, and hardware components to identify vulnerabilities.
- Design Modifications: Update the bootloader to incorporate secure verification processes. This may require modifying the firmware to support cryptographic checks and establishing a Hardware Root of Trust (HRoT) to ensure that only authorized software is executed during the boot process.
- Testing and Validation: Conduct rigorous testing to confirm that the new secure boot implementation does not disrupt the functionality of the equipment. This includes validating that the boot process accurately verifies all software components. It also ensures compliance with the latest FDA cybersecurity guidance.
- Documentation and Compliance: Revise documentation to reflect changes made during the integration process. Ensure that the new design adheres to relevant regulatory standards, which may necessitate additional testing and validation to meet compliance requirements.
- Training and Assistance: Offer extensive instruction for engineering and support groups regarding the new Verified Startup features and their effects on equipment protection and compliance. This is vital for maintaining operational integrity and ensuring that all team members are equipped to handle the updated systems.
By following these steps, manufacturers can effectively implement trusted boot in their existing medical equipment, significantly enhancing security and ensuring adherence to regulatory standards, thereby protecting patient safety. Failure to implement these measures could jeopardize patient safety and regulatory compliance, highlighting the urgent need for action.
Conclusion
Implementing Trusted Boot in medical devices represents a pivotal commitment to patient safety and regulatory compliance. Adopting secure startup processes allows manufacturers to mitigate risks from unauthorized firmware and malicious code, safeguarding sensitive patient data and enhancing medical equipment reliability.
Essential components include the Root of Trust, cryptographic keys, secure bootloaders, and robust firmware update mechanisms. These elements work together to create a comprehensive security framework that meets regulatory requirements and fortifies the integrity of medical devices. The benefits extend beyond compliance, fostering trust among healthcare providers and patients alike, ultimately contributing to better patient outcomes.
As the healthcare landscape evolves, the importance of Trusted Boot cannot be overstated. Manufacturers are urged to prioritize the integration of these security measures into their device designs, recognizing that neglecting these practices can expose devices to significant vulnerabilities, risking patient safety and data integrity. Integrating these security measures not only protects patients but also enhances the overall quality of care provided by medical devices. The failure to adopt these practices could compromise patient safety and undermine the integrity of medical technology.
Frequently Asked Questions
What is the significance of Trusted Boot in medical devices?
Trusted Boot is critical in ensuring that medical devices power on with verified software, safeguarding patient safety and protecting sensitive patient data.
How does Secure Startup contribute to patient safety?
Secure Startup allows manufacturers to block unauthorized firmware, preventing system malfunctions and data breaches, which is essential for maintaining patient safety.
What are the consequences of a medical device failing to verify its software integrity during boot?
If a medical device fails to verify its software integrity, it may run malicious code, endangering patient safety.
Why is the FDA's emphasis on cybersecurity important for medical device manufacturers?
The FDA's emphasis on cybersecurity highlights the need for manufacturers to adopt measures like Secure Startup to protect their products and comply with regulatory requirements.
What operational challenges do manufacturers face regarding key management in medical devices?
Manufacturers face challenges in managing cryptographic keys, especially in environments with many units, making it complex to ensure secure operations.
How might the financial burden of implementing secure boot affect smaller manufacturers?
The financial burden of implementing secure boot may hinder smaller manufacturers, requiring careful budgeting and resource allocation to integrate these security measures.
What does Sudeep Khuraijam emphasize about Trusted Boot?
Sudeep Khuraijam states that Trusted Boot ensures systems start with software that is trusted by the manufacturer, ensuring the operating software is authentic and uncompromised.
What is the projected cybersecurity spending by medical equipment firms by 2027?
Cybersecurity spending by medical equipment firms is expected to reach $1.2 billion by 2027, underscoring the importance of Secure Startup for patient safety and regulatory compliance.
List of Sources
- Understand the Importance of Trusted Boot in Medical Devices
- To Boot Or Not To Boot — Securely: A Medical Device Security Imperative (https://medium.com/@skhuraijam/to-boot-or-not-to-boot-securely-a-medical-device-security-imperative-af3af6fe6bf9)
- FDA could intensify focus on medtech cybersecurity in 2026 (https://medicaldevice-network.com/news/fda-could-intensify-focus-on-medtech-cybersecurity-in-2026)
- The Invisible Guardian: Why Secure Boot is the Pulse of Medical Device Safety (https://gadgeon.com/blog/the-invisible-guardian-why-secure-boot-is-the-pulse-of-medical-device-safety)
- Cybersecurity in Medical Devices: Protecting Patients and Ensuring Trust (https://gadgeon.com/blog/cybersecurity-in-medical-devices-protecting-patients-and-ensuring-trust)
- Identify Key Components for Effective Trusted Boot Implementation
- The Invisible Guardian: Why Secure Boot is the Pulse of Medical Device Safety (https://gadgeon.com/blog/the-invisible-guardian-why-secure-boot-is-the-pulse-of-medical-device-safety)
- To Boot Or Not To Boot — Securely: A Medical Device Security Imperative (https://medium.com/@skhuraijam/to-boot-or-not-to-boot-securely-a-medical-device-security-imperative-af3af6fe6bf9)
- Texas orders cybersecurity review of state agencies for Chinese-made medical devices after federal warnings - Industrial Cyber (https://industrialcyber.co/medical/texas-orders-cybersecurity-review-of-state-agencies-for-chinese-made-medical-devices-after-federal-warnings)
- Cybersecurity in Medical Devices: Protecting Patients and Ensuring Trust (https://gadgeon.com/blog/cybersecurity-in-medical-devices-protecting-patients-and-ensuring-trust)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://health-isac.org/fda-tightens-its-medical-device-cybersecurity-guidance)
- Explore Benefits of Trusted Boot for Regulatory Compliance and Security
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- FDA Urges Medical Device Manufacturers to Improve OT Security (https://hipaajournal.com/fda-medical-device-manufacturers-improve-ot-security)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://health-isac.org/fda-tightens-its-medical-device-cybersecurity-guidance)
- Why many existing medical devices fall short of the FDA's new cybersecurity standards (https://todaysmedicaldevelopments.com/news/why-many-existing-medical-devices-fall-short-fda-new-cybersecurity-standards)
- What to Do About the New FDA Requirements: A CTO's Perspective — Star Lab Software (https://starlab.io/blog/what-to-do-about-the-new-fda-requirements)
- Implement Trusted Boot in Existing Medical Device Designs
- Why many existing medical devices fall short of the FDA's new cybersecurity standards (https://todaysmedicaldevelopments.com/news/why-many-existing-medical-devices-fall-short-fda-new-cybersecurity-standards)
- The Invisible Guardian: Why Secure Boot is the Pulse of Medical Device Safety (https://gadgeon.com/blog/the-invisible-guardian-why-secure-boot-is-the-pulse-of-medical-device-safety)
- FDA Updates Cybersecurity Guidance for Medical Device Makers | 24x7 Magazine posted on the topic | LinkedIn (https://linkedin.com/posts/24x7-biomed_fda-updates-medical-device-cybersecurity-activity-7425651439001055232-YzGq)
- Ensuring Secure Software Updates for Medical Devices | Bold Type (https://boldtype.com/resources/secure-software-updates)
- Cybersecurity (https://fda.gov/medical-devices/digital-health-center-excellence/cybersecurity)