Introduction
In the face of escalating cyber threats, the security of medical devices has become a critical concern for manufacturers. Manufacturers grapple with the complexities of compliance and the evolving landscape of cyber threats, necessitating the adoption of best practices to ensure patient safety. This article outlines strategies that protect vital information and enhance the reliability of healthcare technology.
Understand Unique Security Requirements for Medical Devices
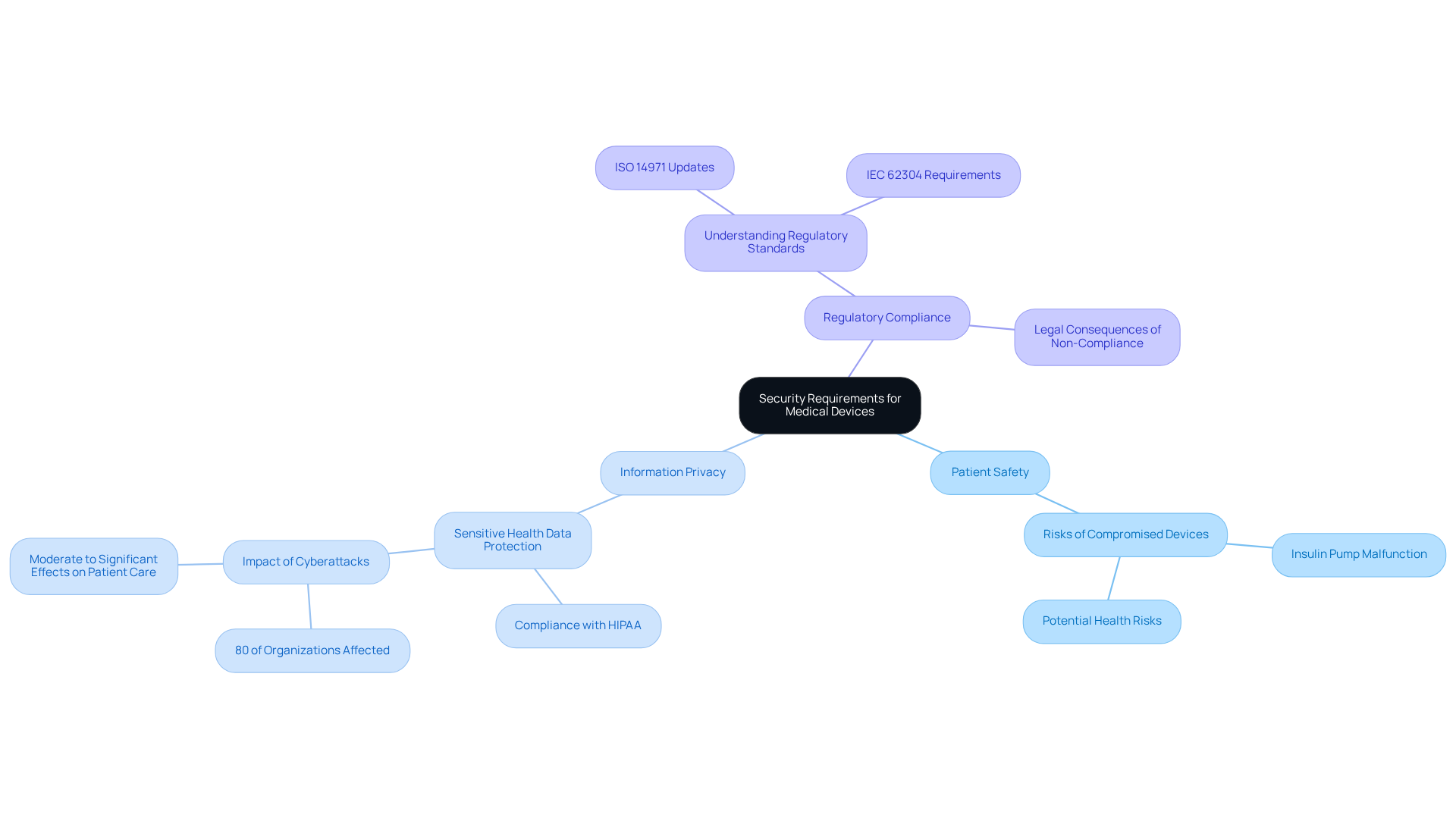
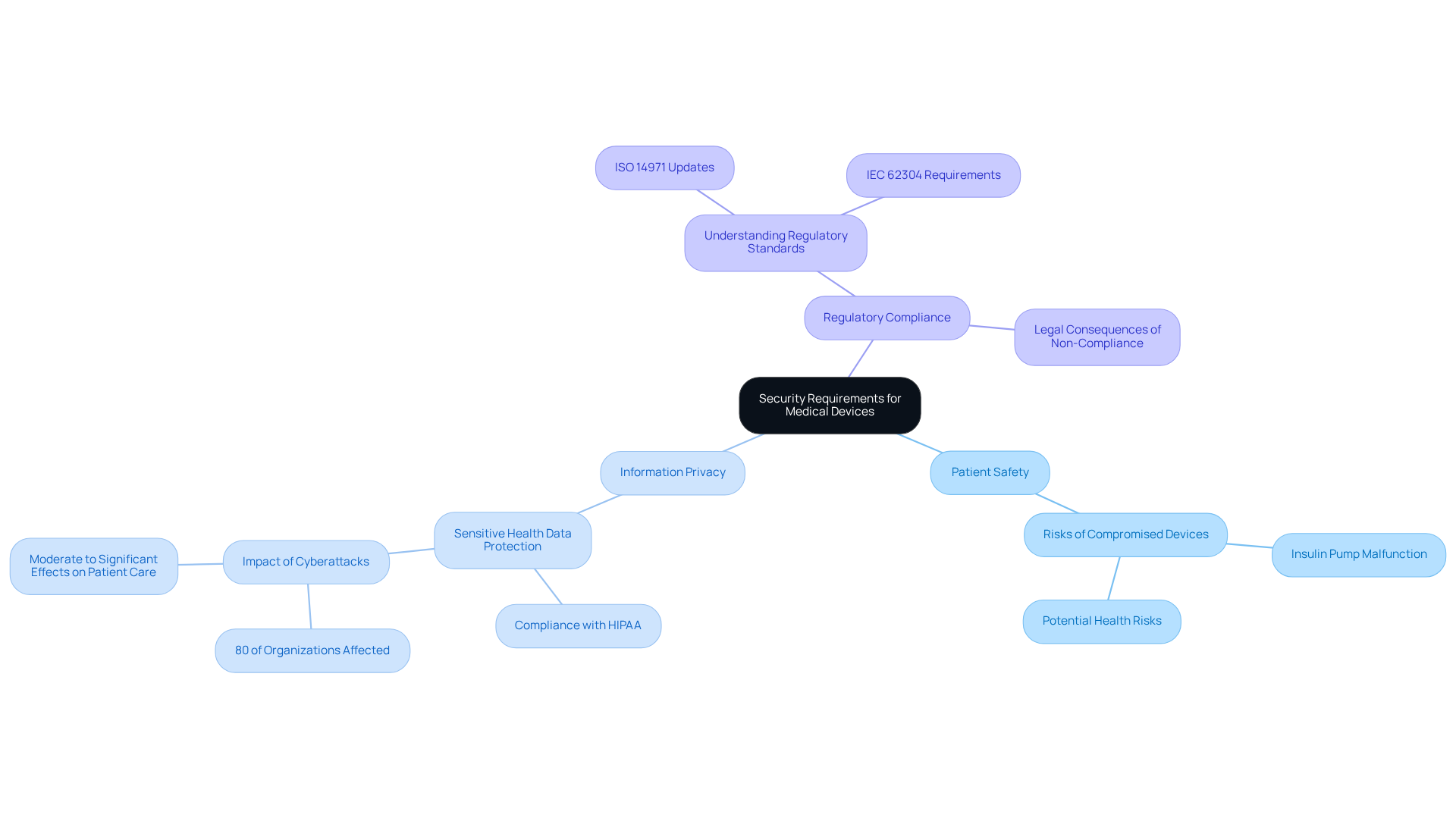
Medical instruments are subject to rigorous regulatory standards that demand meticulous risk assessment and management. Producers face significant challenges in ensuring embedded system security against evolving cyber threats, including unauthorized access and data breaches. Key considerations include:
- Patient Safety: Security measures must be designed to ensure that devices do not jeopardize patient safety. For example, a compromised insulin pump could administer incorrect dosages, leading to severe health risks.
- Information Privacy: Given that healthcare instruments often gather sensitive health details, establishing strong protection measures is essential for adherence to regulations such as HIPAA. In 2026, 80% of organizations impacted by health equipment attacks reported moderate to significant effects on patient care, highlighting the necessity of protecting patient information.
- Regulatory Compliance: A comprehensive grasp of the particular rules overseeing healthcare instruments is essential for guaranteeing adherence and evading legal consequences. Recent updates to ISO 14971 and IEC 62304 stress the necessity for producers to incorporate embedded system security into the design and lifecycle of their products, proactively addressing vulnerabilities.
Addressing these critical needs is essential for producers to navigate the complexities of the healthcare landscape effectively.
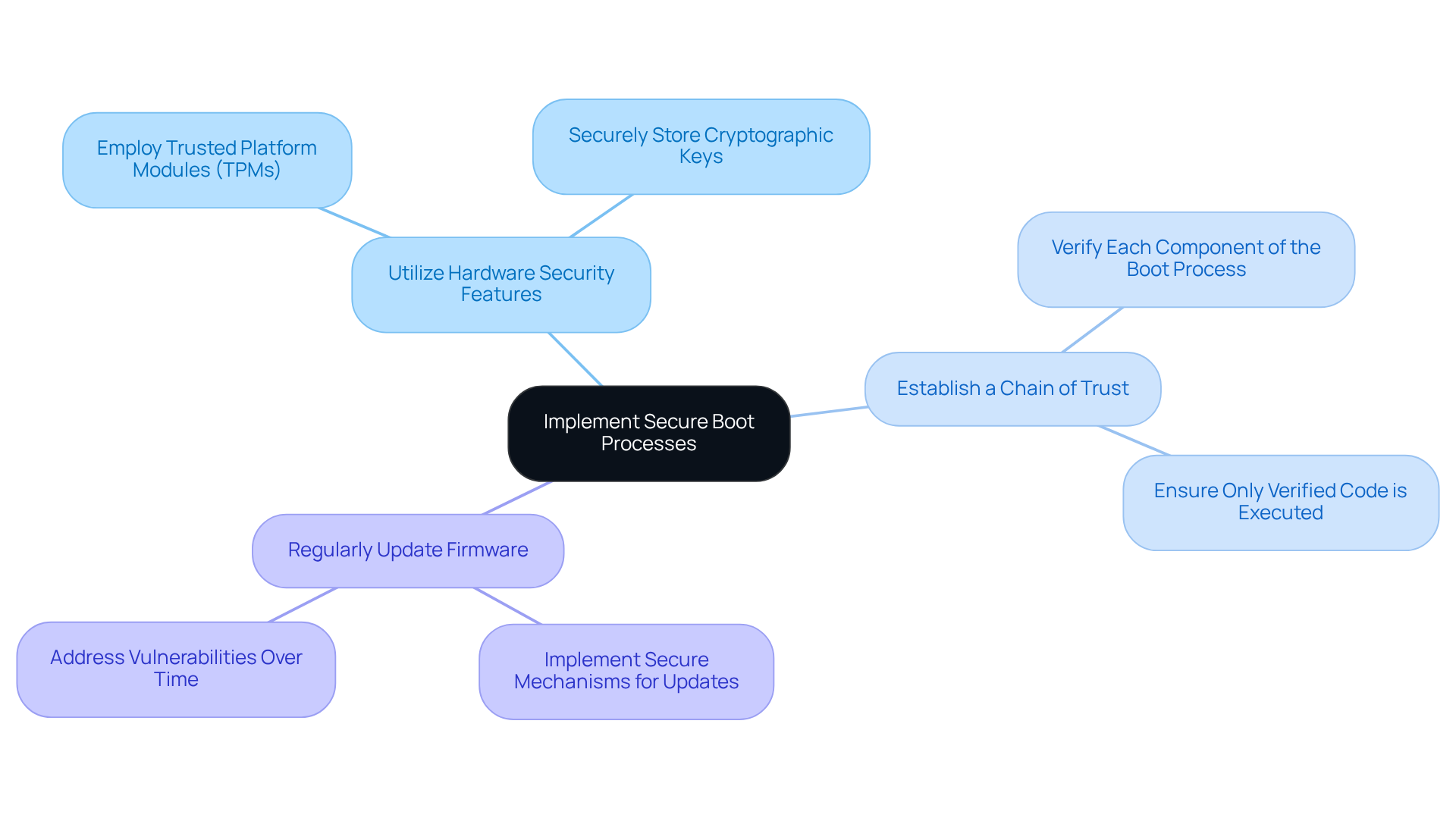
Implement Secure Boot Processes
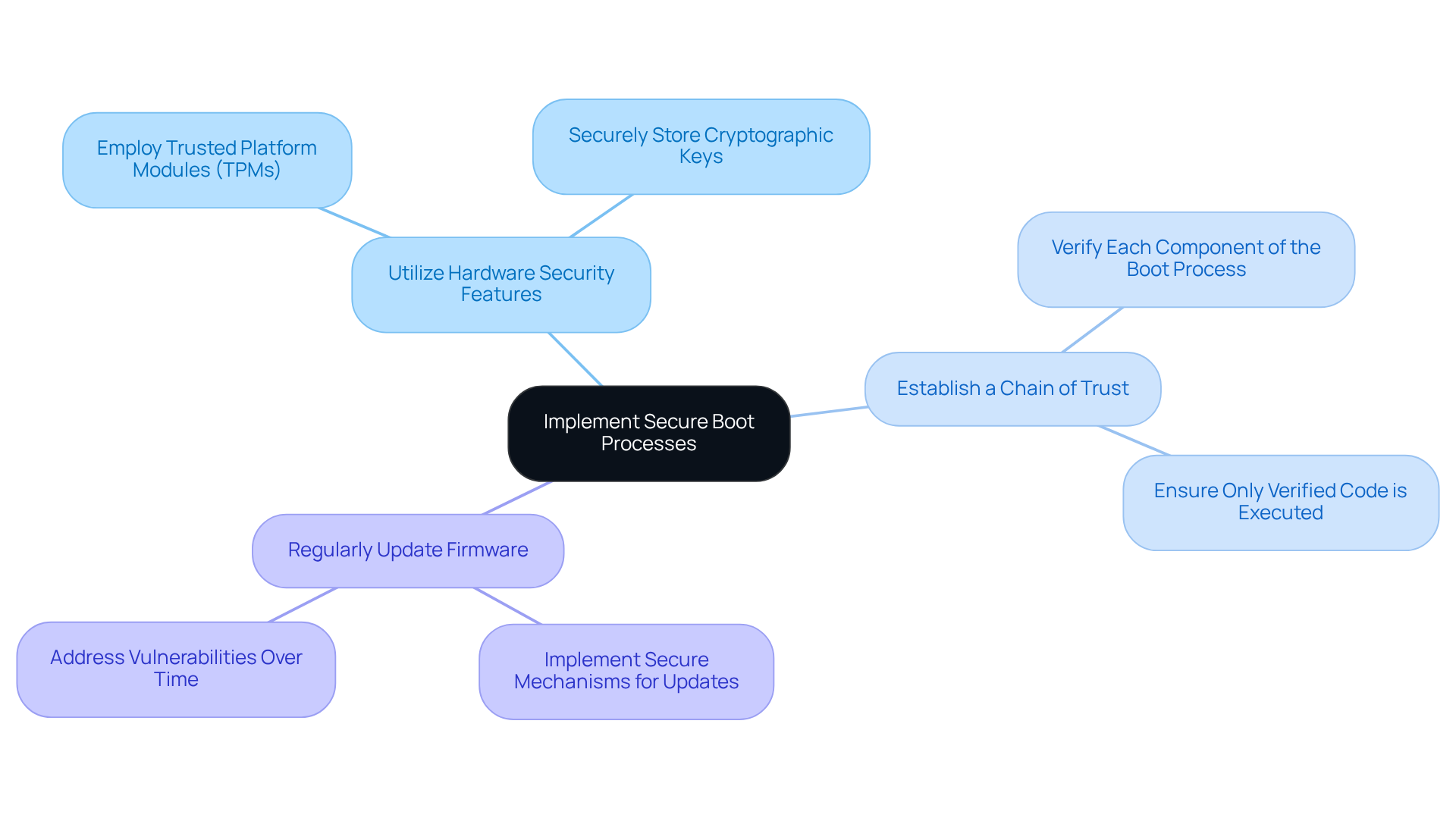
In the realm of medical equipment, the absence of secure boot can lead to significant vulnerabilities, jeopardizing patient safety and regulatory compliance. Secure boot is a critical security feature that ensures only authenticated and authorized software is executed during the boot process. To effectively implement secure boot, manufacturers must focus on three key strategies:
- Utilize Hardware Security Features: Employ hardware-based security elements, such as Trusted Platform Modules (TPMs) or secure elements, to securely store cryptographic keys, thereby enhancing the integrity of the device.
- Establish a Chain of Trust: Develop a robust chain of trust that verifies each component of the boot process, ensuring that only verified code is executed, which is essential for maintaining the security of the system.
- Regularly Update Firmware: Implement secure mechanisms for firmware updates to address vulnerabilities and enhance security over time, ensuring that equipment remains resilient against emerging threats.
The implementation of secure boot is not merely a technical enhancement; it is a critical step towards safeguarding patient welfare and meeting regulatory demands.
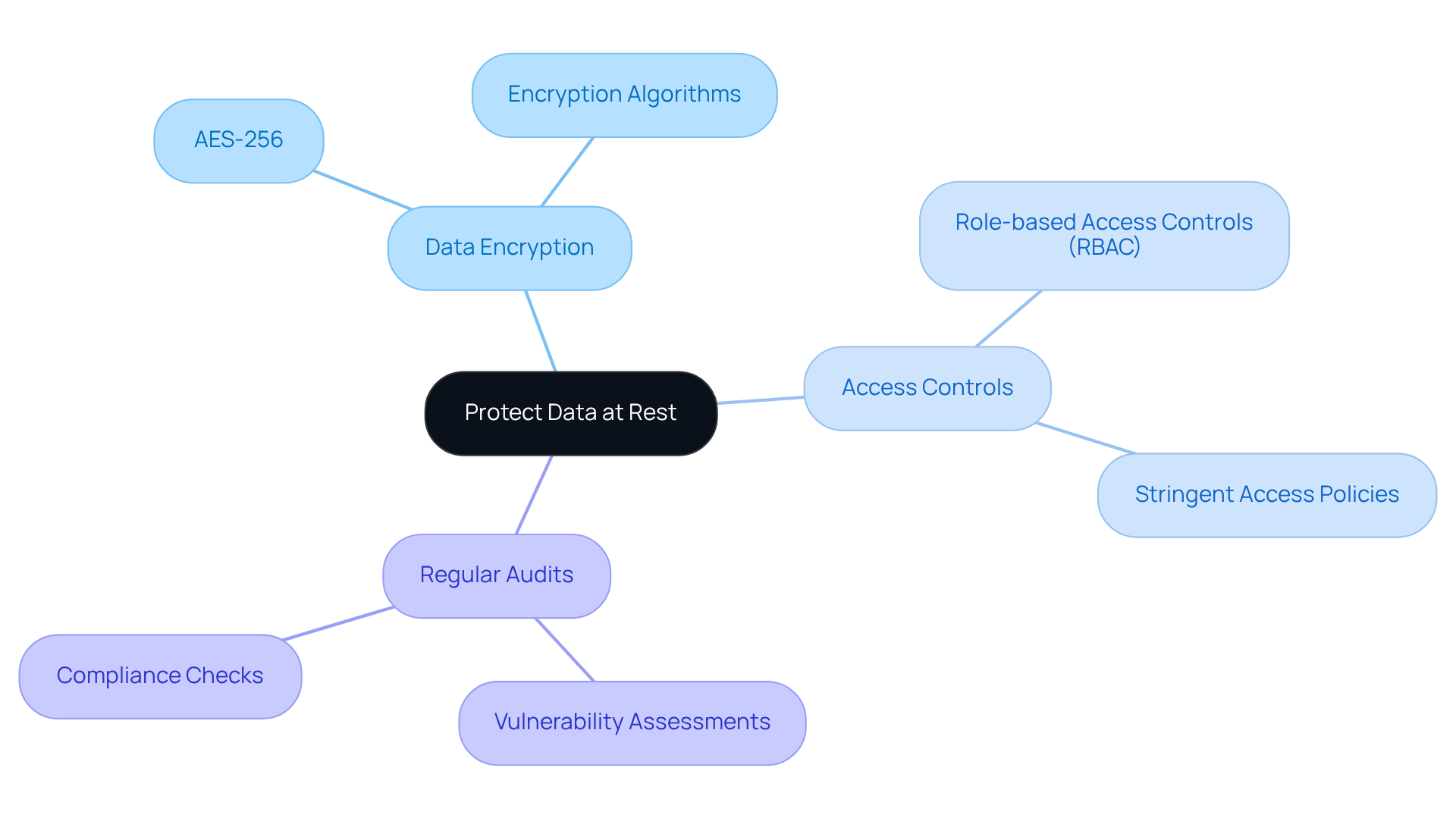
Protect Data at Rest
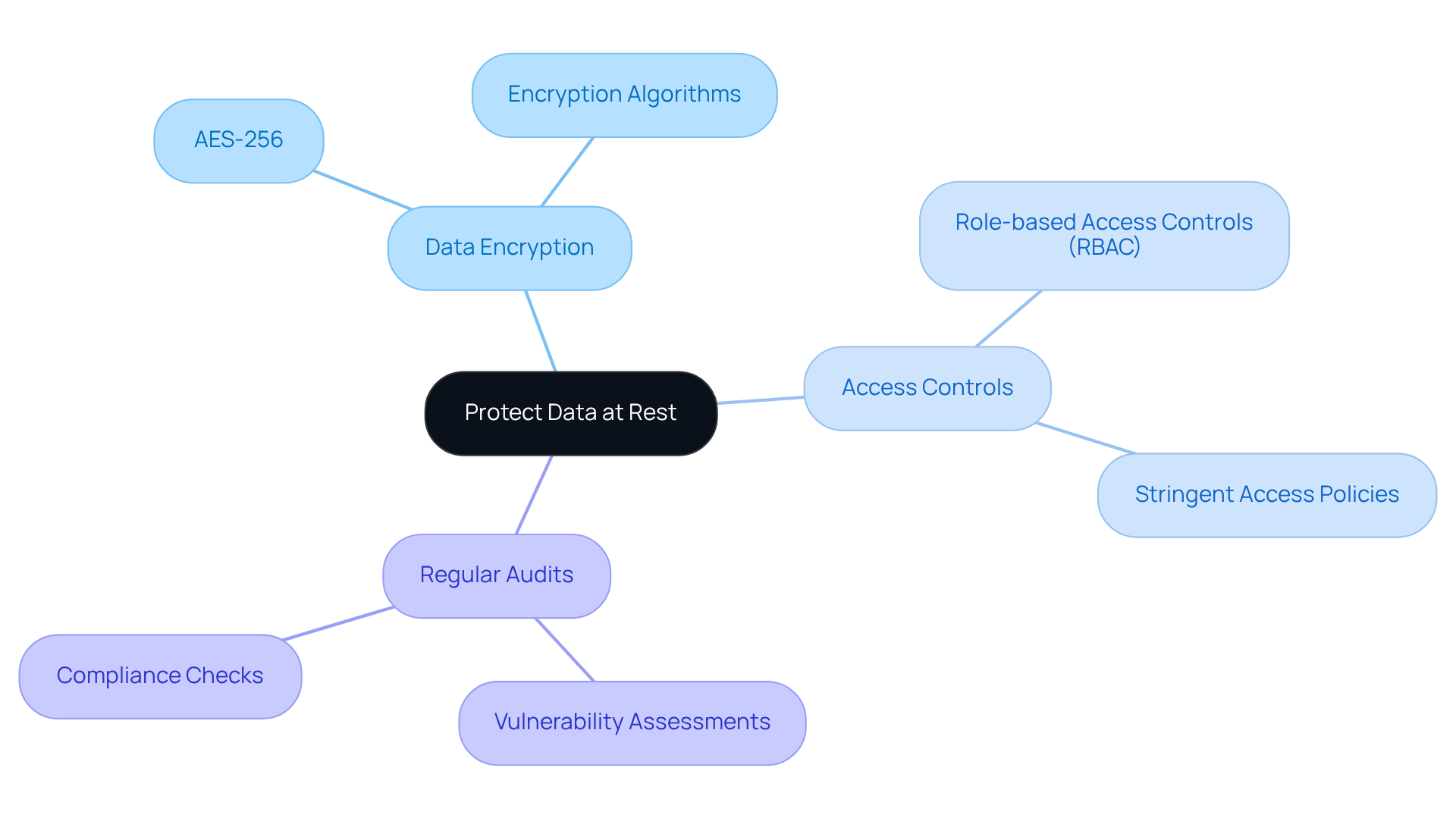
To effectively protect sensitive data on medical devices, manufacturers must adopt comprehensive security measures that address potential vulnerabilities:
- Data Encryption: Employing robust encryption algorithms, like AES-256, is crucial for safeguarding data at rest. This ensures that even in the event of unauthorized access, the information remains unreadable.
- Access Controls: Establishing stringent access controls is vital to ensure that only authorized personnel can access sensitive information. Role-based access controls (RBAC) can help maintain this security.
- Regular Audits: Regular security audits are essential for identifying and mitigating vulnerabilities in information storage practices.
By implementing these measures, manufacturers can significantly mitigate the risks associated with data breaches, thereby enhancing the embedded system security and overall reliability of their medical devices.
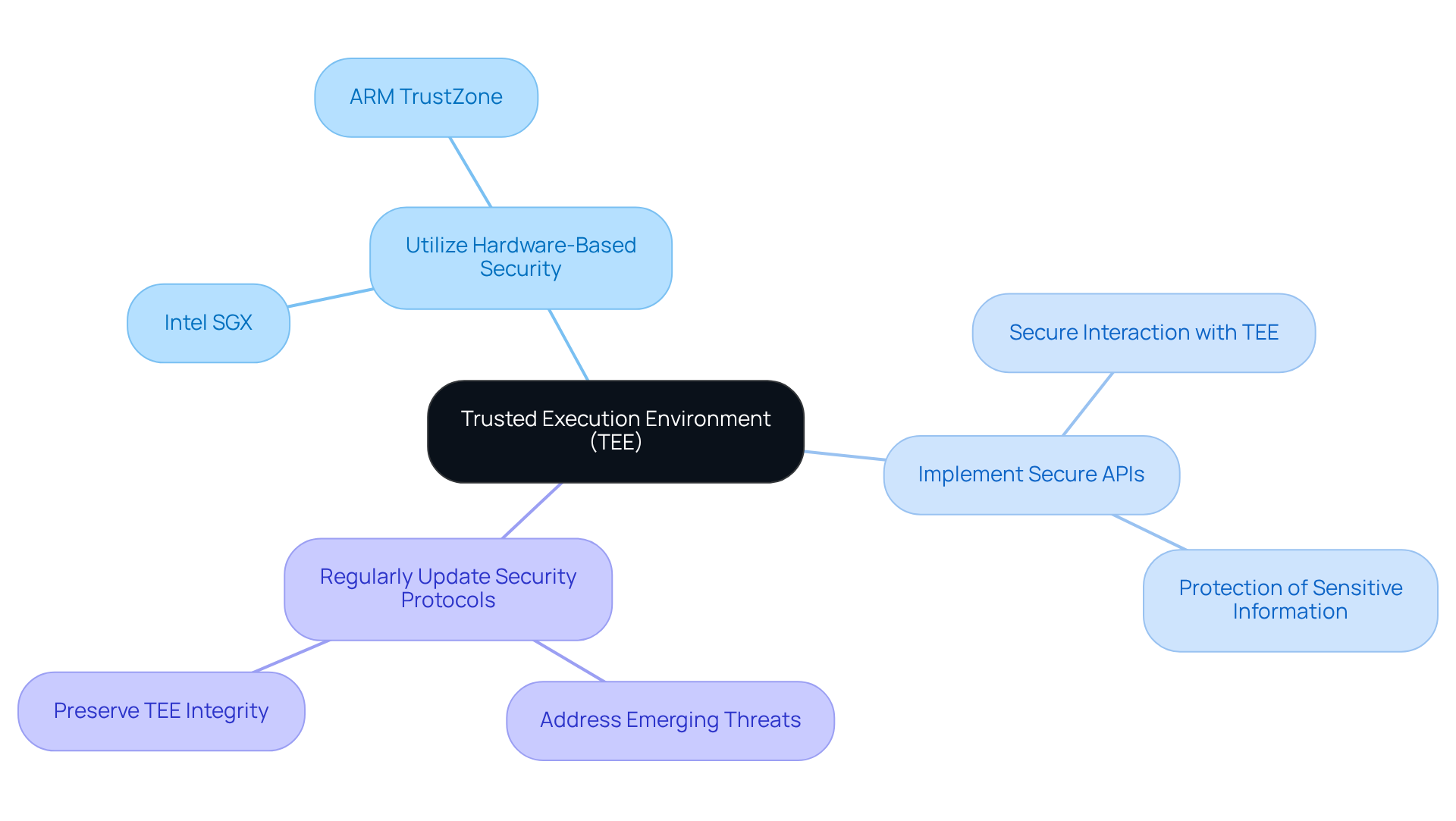
Establish a Trusted Execution Environment
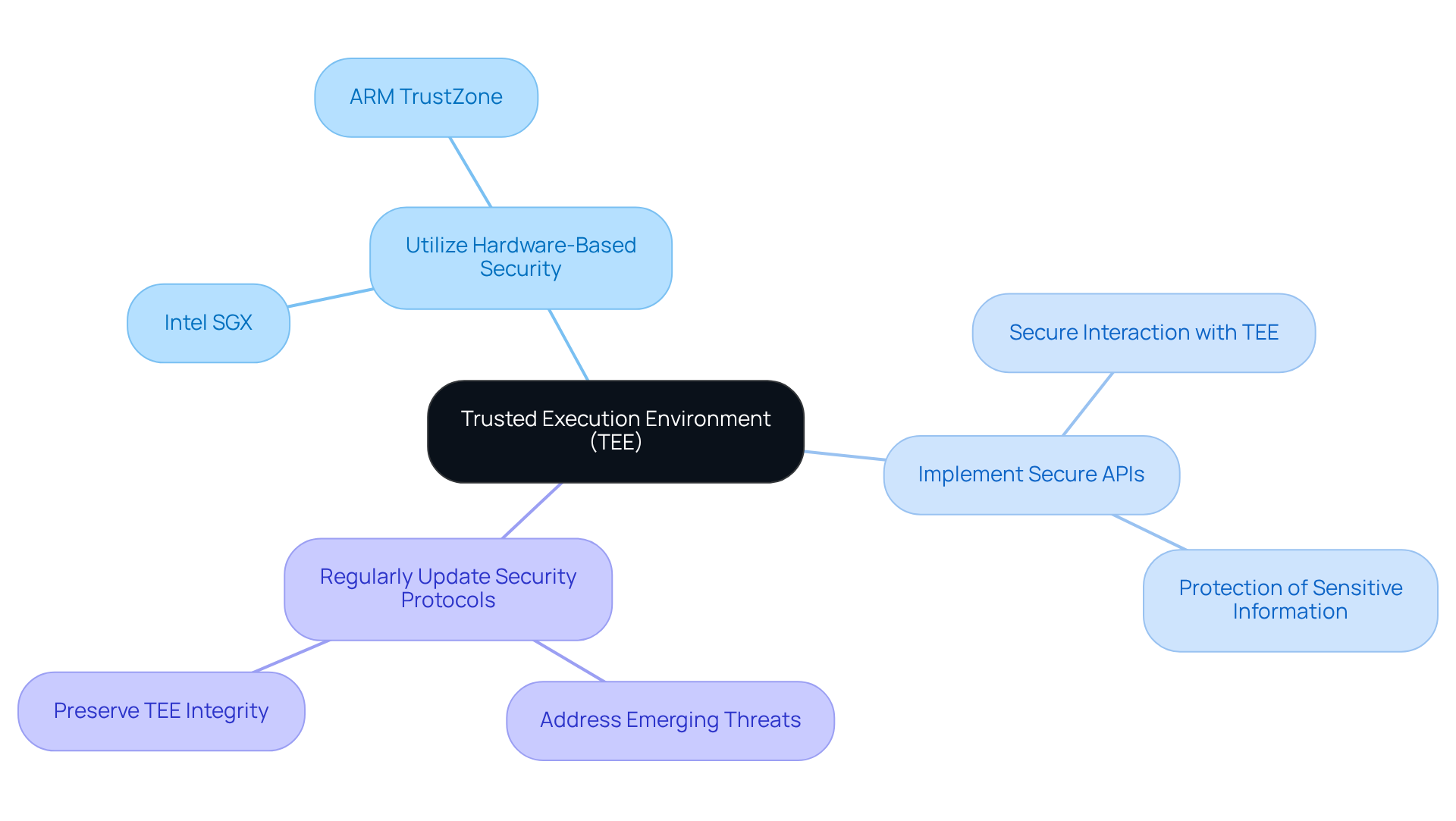
In an era where cyber threats are increasingly sophisticated, establishing a Trusted Execution Environment (TEE) is crucial for safeguarding sensitive information within medical devices. A TEE offers a secure zone within a device's processor, protecting sensitive information and operations from unauthorized access. To establish a TEE effectively, manufacturers must focus on these key practices:
Implementing a TEE not only protects sensitive data but also builds trust in medical devices among users and stakeholders. The global TEE market is projected to reach approximately USD 18.1 billion by 2033, reflecting the growing recognition of the importance of secure computing environments in healthcare. As the demand for secure computing environments grows, the implementation of TEEs will be pivotal in maintaining the integrity of healthcare technology and patient trust.
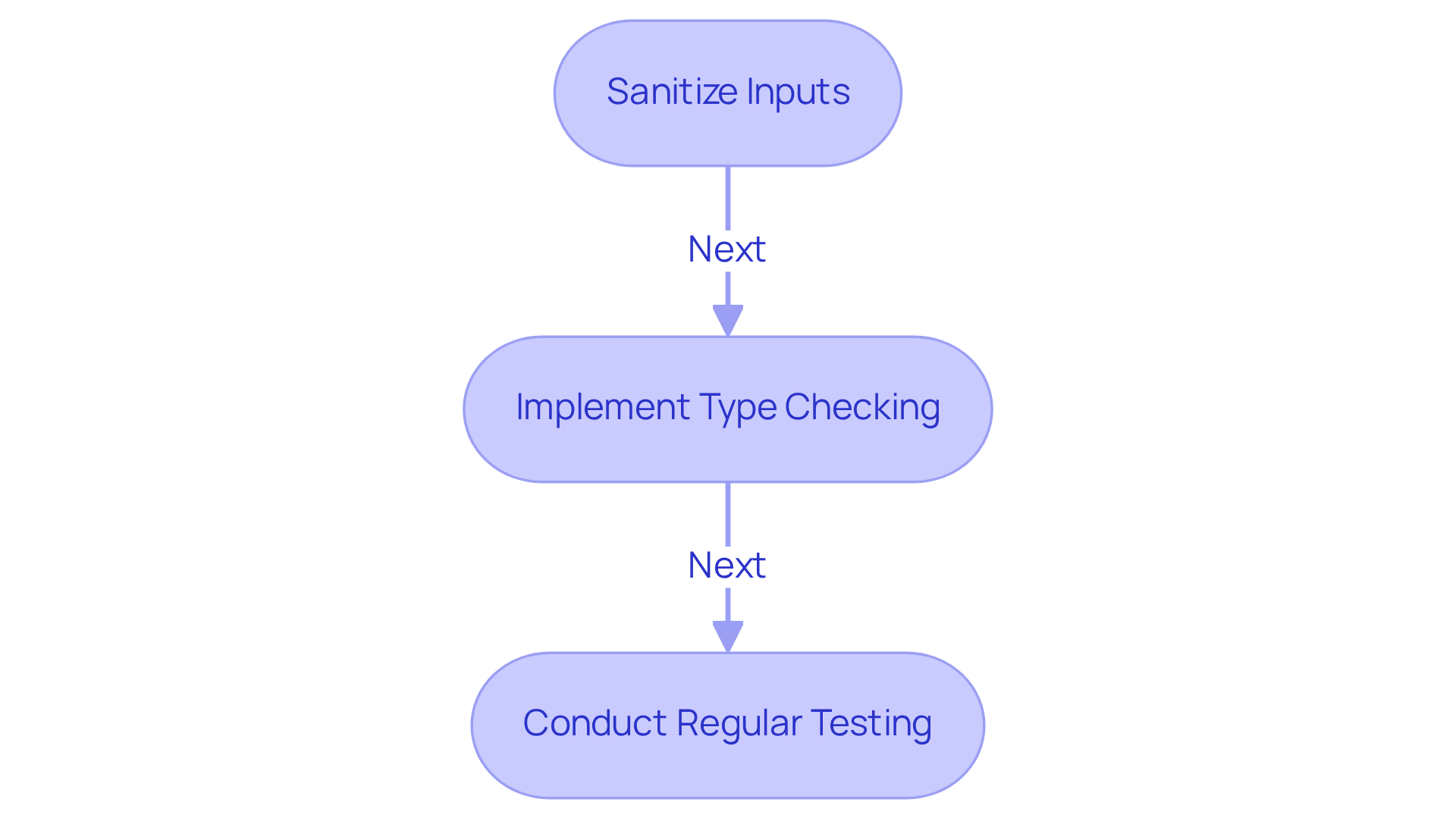
Improper data handling poses significant risks to the embedded system security and overall reliability of medical devices. Manufacturers should adopt the following best practices for data input validation:
Neglecting these best practices could jeopardize patient safety and the effectiveness of medical devices.
Conclusion
The security of embedded systems in medical devices is critical for patient safety and trust in healthcare technologies. Manufacturers must identify and address the unique security needs of medical devices to comply with regulatory standards. This commitment is essential for patient safety, information privacy, and regulatory compliance.
Key practices include:
- Implementing secure boot processes
- Protecting data at rest
- Establishing a Trusted Execution Environment
- Validating all data inputs
These measures are critical for fortifying the security framework of medical devices.
As healthcare technology evolves, embedded system security remains paramount. Enhancing security allows stakeholders to foster a safer healthcare environment focused on patient well-being and data integrity.
Frequently Asked Questions
What are the unique security requirements for medical devices?
Medical devices must meet rigorous regulatory standards that focus on risk assessment and management, ensuring patient safety, information privacy, and regulatory compliance against evolving cyber threats.
Why is patient safety a critical consideration in medical device security?
Security measures must ensure that devices do not compromise patient safety, as a compromised device, like an insulin pump, could administer incorrect dosages, posing severe health risks.
How does information privacy relate to medical device security?
Medical devices often collect sensitive health information, making strong protection measures necessary to comply with regulations such as HIPAA. In 2026, many organizations reported significant impacts on patient care due to health equipment attacks, underscoring the importance of safeguarding patient information.
What regulatory requirements must medical device manufacturers adhere to?
Manufacturers must understand specific regulations governing healthcare instruments to ensure compliance and avoid legal issues. Updates to ISO 14971 and IEC 62304 emphasize the need for integrating embedded system security throughout the product's design and lifecycle.
What is secure boot in the context of medical devices?
Secure boot is a security feature that ensures only authenticated and authorized software is executed during the boot process, preventing significant vulnerabilities that could jeopardize patient safety and regulatory compliance.
What strategies should manufacturers implement for secure boot?
Manufacturers should utilize hardware security features, establish a chain of trust to verify boot components, and regularly update firmware to address vulnerabilities and enhance security.
Why is the implementation of secure boot important for medical devices?
Implementing secure boot is crucial for safeguarding patient welfare and meeting regulatory demands, as it ensures the integrity and security of the device from the moment it powers on.
List of Sources
- Understand Unique Security Requirements for Medical Devices
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- Medical Device Cybersecurity in 2026: More Investment, More Attacks, More Harm (https://cybrsecmedia.com/medical-device-cybersecurity-in-2026-more-investment-more-attacks-more-harm)
- Healthcare Cybersecurity Statistics 2026 Report (https://ordr.net/healthcare-cybersecurity-statistics)
- Implement Secure Boot Processes
- Medical Device Cybersecurity in 2026: More Investment, More Attacks, More Harm (https://cybrsecmedia.com/medical-device-cybersecurity-in-2026-more-investment-more-attacks-more-harm)
- 4 Best Practices for Implementing Trusted Boot in Medical Devices (https://volersystems.com/blog/4-best-practices-for-implementing-trusted-boot-in-medical-devices)
- RunSafe Security Releases 2026 Medical Device Cybersecurity Index as Attacks Impacting Medical Devices Rise and Procurement Standards Tighten (https://businesswire.com/news/home/20260429787733/en/RunSafe-Security-Releases-2026-Medical-Device-Cybersecurity-Index-as-Attacks-Impacting-Medical-Devices-Rise-and-Procurement-Standards-Tighten)
- FDA Cybersecurity Guidance 2026: What Changed? (https://hattrick-it.com/blog/cybersecurityguidanceupdate)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- Protect Data at Rest
- RunSafe Security Releases 2026 Medical Device Cybersecurity Index as Attacks Impacting Medical Devices Rise and Procurement Standards Tighten (https://businesswire.com/news/home/20260429787733/en/RunSafe-Security-Releases-2026-Medical-Device-Cybersecurity-Index-as-Attacks-Impacting-Medical-Devices-Rise-and-Procurement-Standards-Tighten)
- Healthcare Cybersecurity Statistics 2026 Report (https://ordr.net/healthcare-cybersecurity-statistics)
- 80+ Healthcare Data Breach Statistics 2026 (https://getastra.com/blog/security-audit/healthcare-data-breach-statistics)
- FDA could intensify focus on medtech cybersecurity in 2026 (https://medicaldevice-network.com/news/fda-could-intensify-focus-on-medtech-cybersecurity-in-2026)
- Healthcare Data Security in 2026: Protecting Sensitive Medical Information (https://eccu.edu/blog/healthcare-data-security-in-2026)
- Establish a Trusted Execution Environment
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://health-isac.org/fda-tightens-its-medical-device-cybersecurity-guidance)
- Trusted Execution Environment Market Research Report 2033 (https://dataintelo.com/report/trusted-execution-environment-market)
- FDA Tightens Its Medical Device Cybersecurity Guidance (https://fedtechmagazine.com/article/2026/03/fda-tightens-its-medical-device-cybersecurity-guidance-perfcon)
- FDA could intensify focus on medtech cybersecurity in 2026 (https://medicaldevice-network.com/news/fda-could-intensify-focus-on-medtech-cybersecurity-in-2026)
- Validate All Data Inputs
- FDA Cybersecurity Guidance 2026: What Changed? (https://hattrick-it.com/blog/cybersecurityguidanceupdate)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- FDA Updates Broaden Wellness and Clinical Decision Support Software Devices Under Enforcement (https://emergobyul.com/news/fda-updates-broaden-wellness-and-clinical-decision-support-software-devices-under-enforcement)
- A QMSR State of Mind: FDA Adopts New Inspection Approach for Medical Devices as Quality Management System Regulation Takes Effect | Insights | Ropes & Gray LLP (https://ropesgray.com/en/insights/alerts/2026/02/a-qmsr-state-of-mind-fda-adopts-new-inspection-approach-for-medical-devices)
- Product, Equipment/Process, Software and QMS Verification and Validation Webinar: Compliance Strategies for Medical Devices, Pharmaceuticals, Diagnostics and Biologics (July 6th - July 7th, 2026) (https://globenewswire.com/de/news-release/2026/04/29/3283887/0/en/product-equipment-process-software-and-qms-verification-and-validation-webinar-compliance-strategies-for-medical-devices-pharmaceuticals-diagnostics-and-biologics-july-6th-july-7th.html)