Best Practices for Cyber Security in Embedded Systems for Medical Devices
Explore best practices for cyber security embedded systems in medical devices to enhance...

The rapid advancement of medical technology necessitates enhanced security measures, particularly in the embedded software that powers medical devices. As the healthcare landscape becomes increasingly digital, the stakes for ensuring patient safety and regulatory compliance rise significantly. This article examines essential best practices that manufacturers can adopt to strengthen embedded software security, exploring strategies that not only protect sensitive data but also safeguard human lives.
How can organizations effectively integrate these security measures from the outset of development to mitigate risks and enhance the reliability of their products?
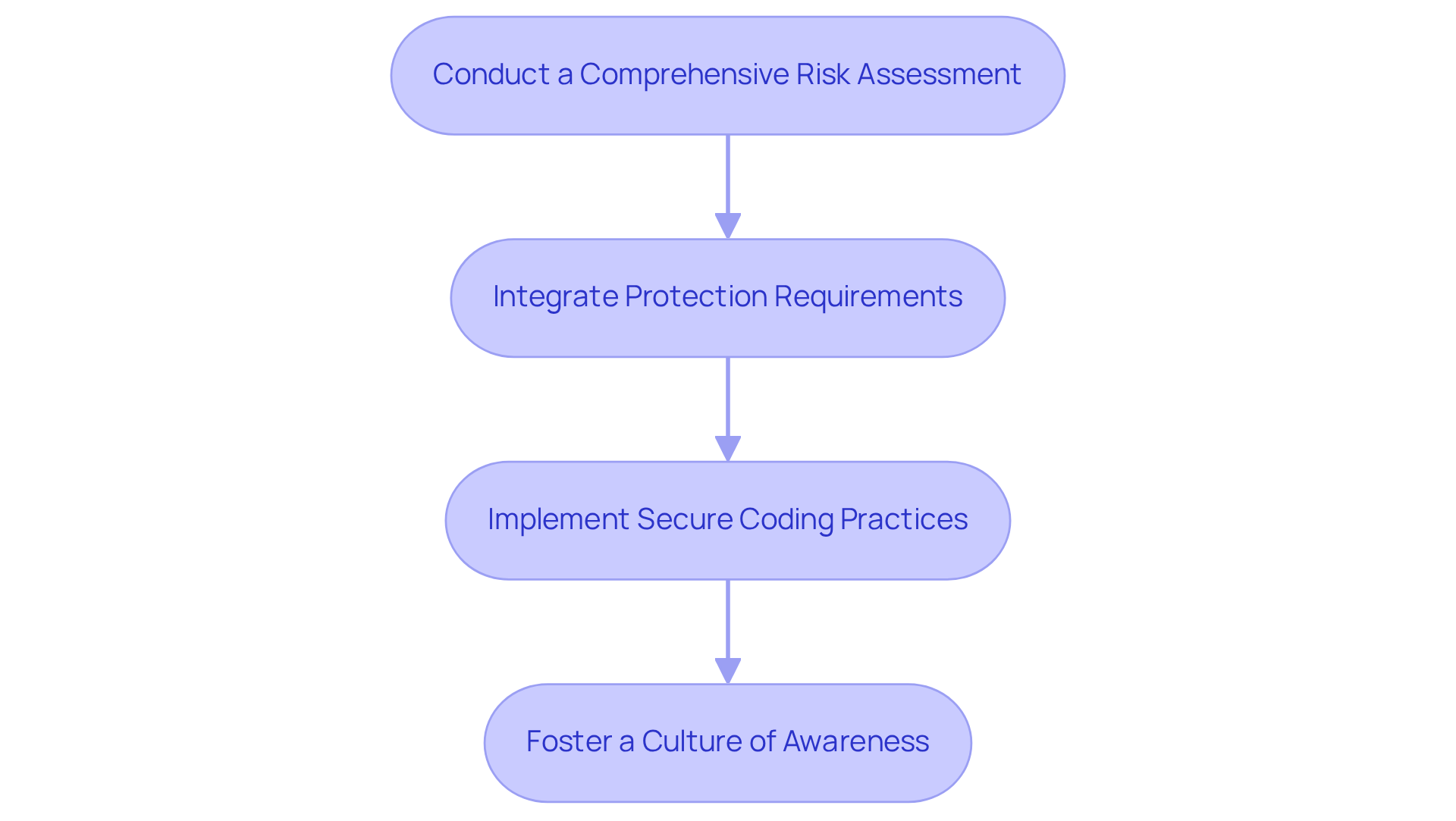
To ensure in , it is essential to prioritize protection from the outset of the development process. This involves several critical steps:
As the landscape of medical equipment development evolves, incorporating protection from the beginning is not merely a best practice; it is vital for ensuring and maintaining regulatory compliance. For instance, the FDA's approval of an Apple Watch-enabled system for seizure monitoring in April 2025 underscores the growing market for remote monitoring solutions, highlighting the necessity of . Moreover, with 77% of healthcare organizations targeted by ransomware in the past year, addressing common oversights-such as neglecting updates for outdated systems and failing to -can significantly enhance and equipment protection. By proactively addressing these issues, manufacturers can better safeguard their products and patients.
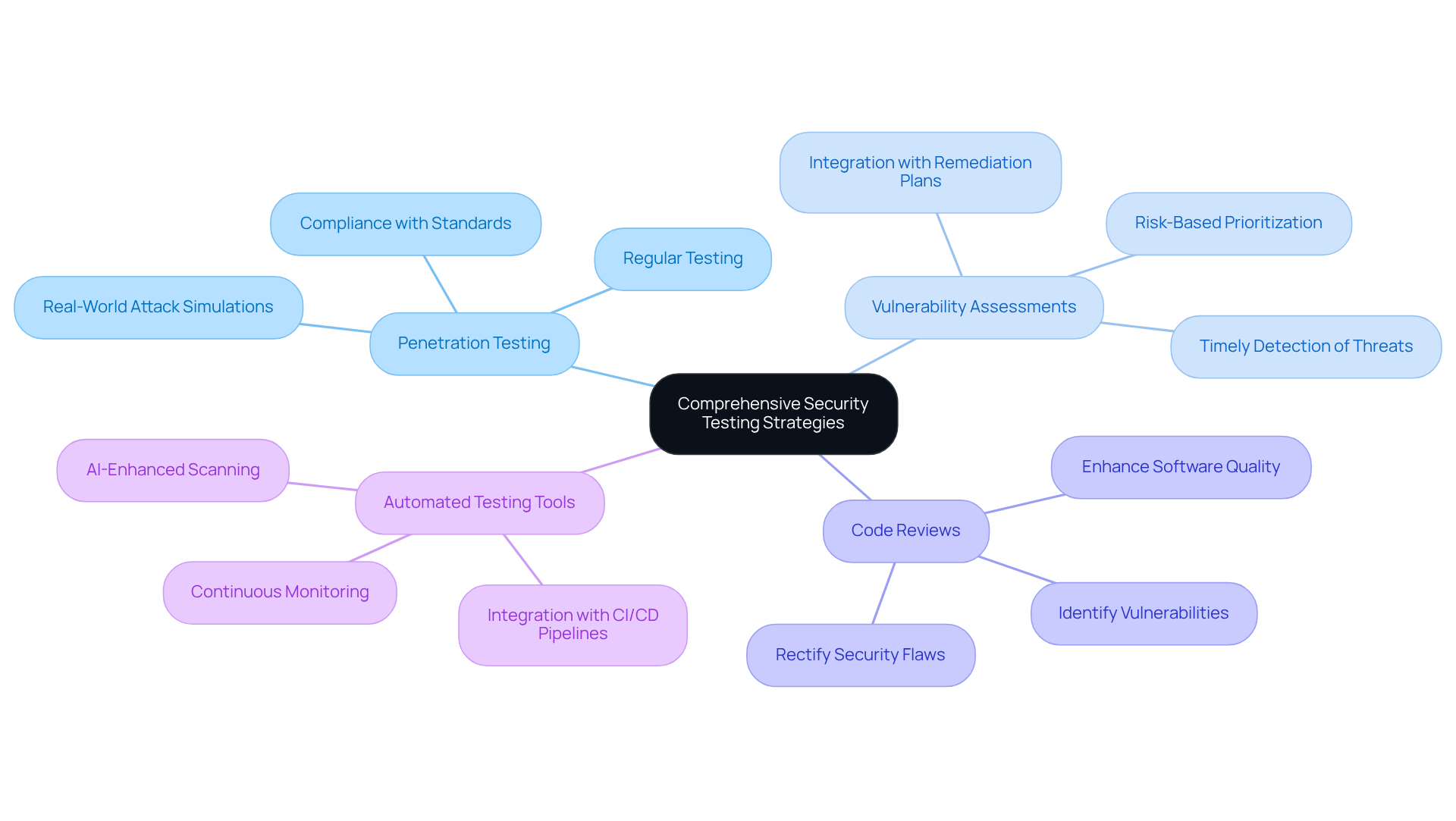
To effectively safeguard in medical devices, organizations must implement a . This strategy should encompass:
The use of can facilitate continuous monitoring and evaluation of the software's safety posture, ensuring timely detection of potential threats. Additionally, incorporating provides essential insights into the software's resilience against genuine cyber threats. By establishing a , manufacturers can not only achieve but also enhance and the overall reliability of their in an increasingly complex cyber landscape.
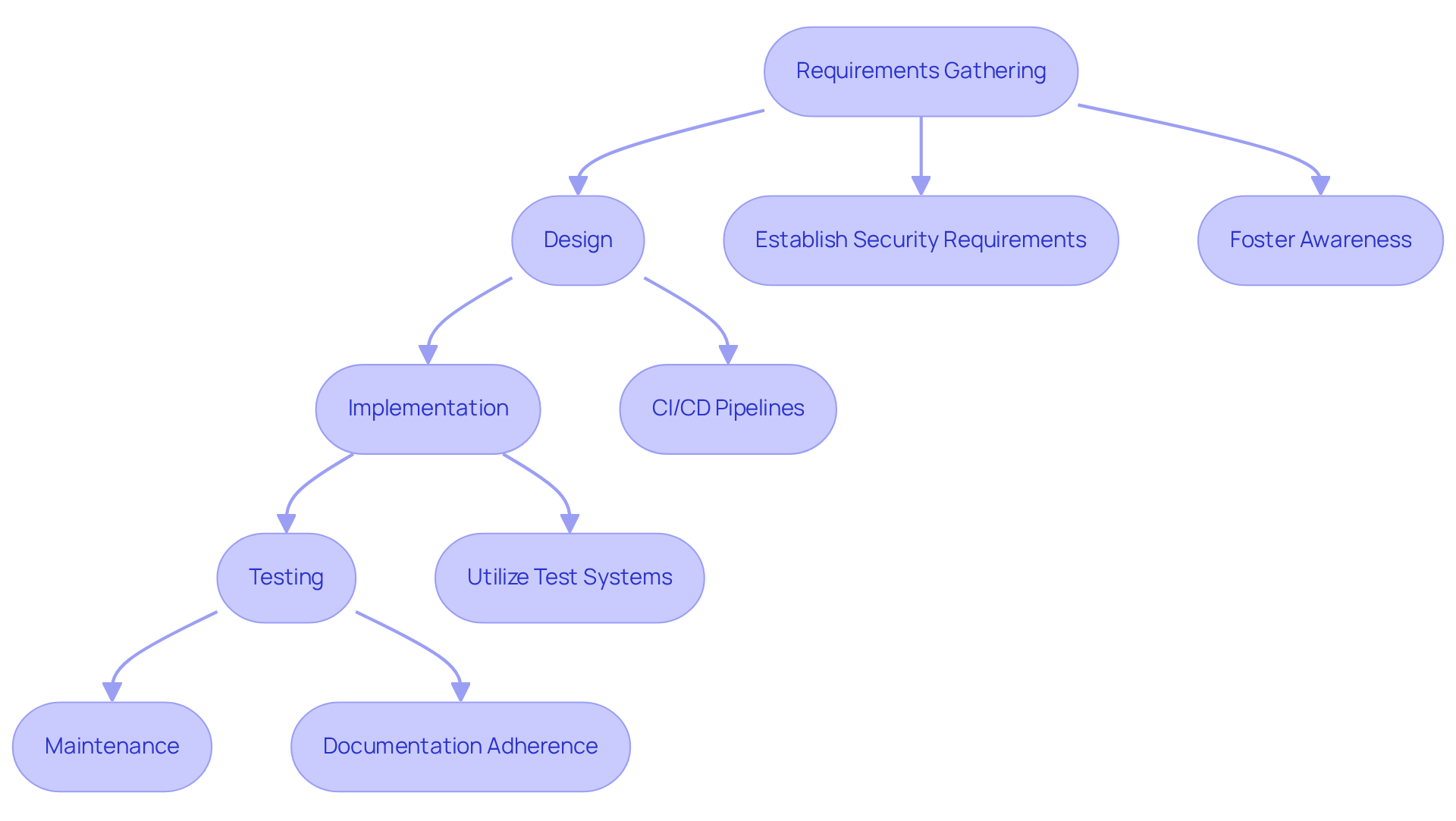
Integrating a is essential for safeguarding in medical devices. This approach necessitates the incorporation of measures at every stage of the (SDLC), which includes requirements gathering, design, implementation, testing, and maintenance.
Key Practices:
A systematic, security-first development strategy can lead to quicker regulatory approvals and improved clinical outcomes, positioning organizations as leaders in innovation within the healthcare sector. As Vincent Balgos states, 'It is not only a best practice, but a moral obligation for medical equipment teams to incorporate protection into the DNA of their development process.'
Moreover, with the average cost of a security breach in the United States reaching $9.44 million, the stakes for implementing robust security measures are higher than ever. By adopting these practices, organizations can not only safeguard their equipment but also build trust with healthcare providers and patients.
Furthermore, utilizing test systems during the development process ensures that products meet rigorous quality and reliability criteria, which is vital for managing adherence from prototype to production in . Additionally, addressing documentation adherence and user guides is crucial for overcoming regulatory challenges faced by .
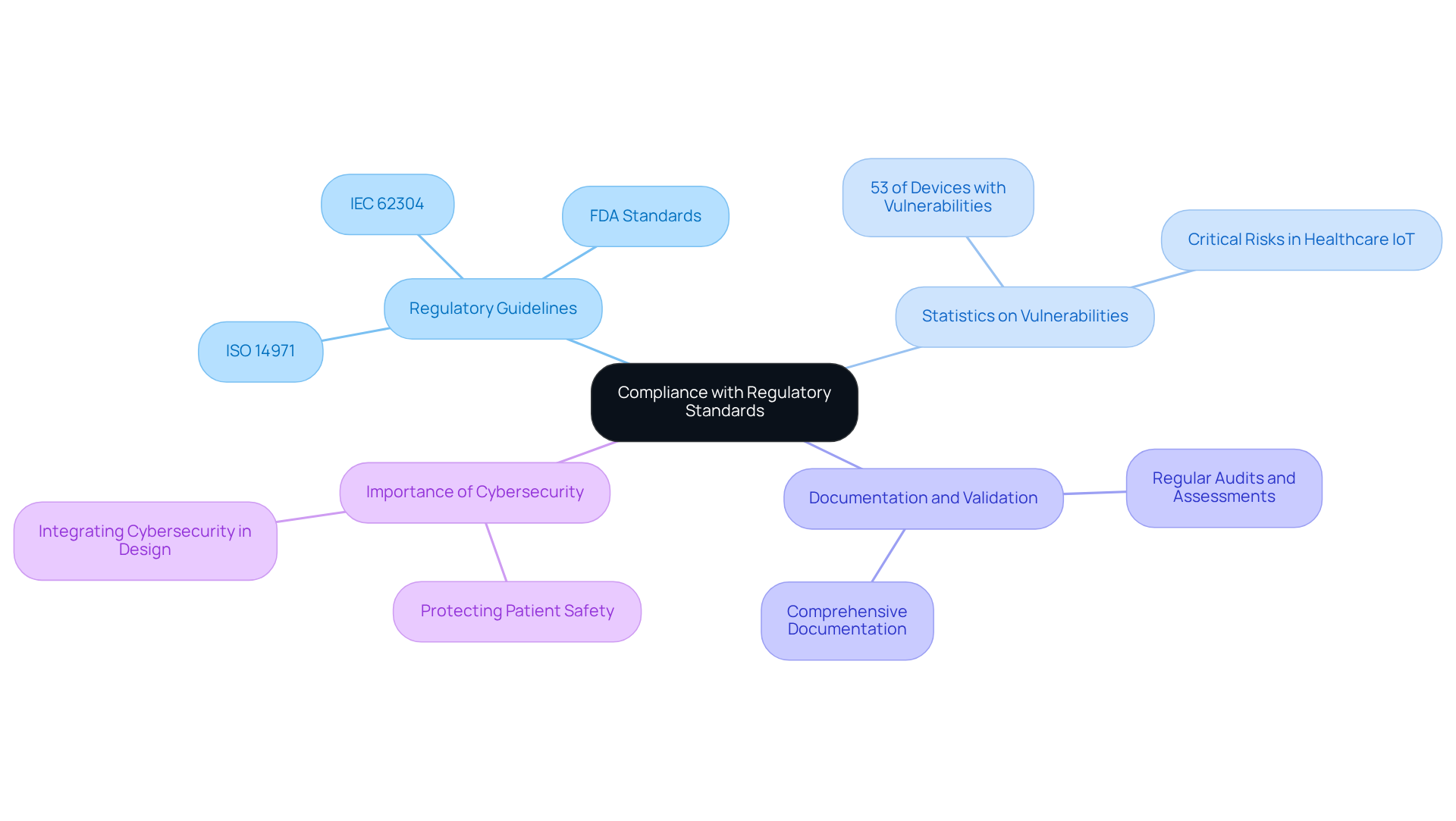
To ensure the safety and efficiency of integrated software in healthcare equipment, adherence to applicable and established practices is essential. This includes compliance with standards set by organizations such as the . Recent updates from the FDA, dated January 6, 2026, underscore the importance for manufacturers to stay informed about regulatory requirements. Notably, statistics indicate that 53% of connected medical devices in hospitals exhibit recognized critical vulnerabilities, which emphasizes the need for and robust protective measures.
Manufacturers must engage in to demonstrate . Regular audits and assessments are vital for identifying areas for improvement and ensuring that measures remain current.
As Christian Espinosa, founder and CEO of Blue Goat Cyber, articulates, " is not just about protecting data; it’s about safeguarding human lives." By prioritizing compliance, organizations such as can enhance device safety and foster trust among stakeholders and end-users.
Prioritizing embedded software security in medical devices is not merely a strategic advantage; it is essential for safeguarding patient health and ensuring regulatory compliance. By embedding security measures from the outset of the development process, manufacturers can establish a robust framework that effectively addresses potential risks and vulnerabilities.
This article outlines several best practices, including:
Emphasizing a security-first approach throughout the software development lifecycle ensures that every stage-from requirements gathering to maintenance-is fortified against emerging threats. Furthermore, compliance with regulatory standards is crucial, as it not only enhances device safety but also builds trust with stakeholders.
As the landscape of healthcare technology continues to evolve, the significance of robust embedded software security cannot be overstated. Organizations must take proactive steps to address vulnerabilities and ensure compliance with the latest guidelines. By doing so, they not only protect their products but also contribute to a safer healthcare environment for all. The call to action is clear: prioritize security in every aspect of medical device development to safeguard lives and foster innovation.
Why is it important to prioritize embedded software security in medical devices from the start?
Prioritizing embedded software security from the outset is crucial for ensuring patient safety and maintaining regulatory compliance throughout the product lifecycle.
What are the critical steps to ensure embedded software security in medical devices?
The critical steps include conducting a comprehensive risk assessment, integrating protection requirements into design specifications, implementing secure coding practices, and fostering a culture of awareness among team members.
What is the purpose of conducting a comprehensive risk assessment?
A comprehensive risk assessment helps identify potential vulnerabilities and threats before any coding begins, allowing for proactive measures to be taken.
How can protection requirements be integrated into the development process?
Protection requirements can be embedded into the initial design specifications to establish a robust framework that addresses safety concerns throughout the product lifecycle.
What role do secure coding practices play in embedded software security?
Secure coding practices and threat modeling techniques are utilized to anticipate and effectively mitigate risks, enhancing the overall security of the software.
Why is fostering a culture of awareness important in embedded software security?
Cultivating a culture of awareness regarding safety among all team members enhances the project's overall protection posture and ensures that security is a shared responsibility.
What recent example highlights the need for robust protective measures in medical device development?
The FDA's approval of an Apple Watch-enabled system for seizure monitoring in April 2025 underscores the growing market for remote monitoring solutions and the necessity of robust protective measures.
What alarming statistic emphasizes the importance of addressing embedded software security?
A statistic indicates that 77% of healthcare organizations were targeted by ransomware in the past year, highlighting the need for improved security measures.
What common oversights should manufacturers address to enhance embedded software security?
Manufacturers should address common oversights such as neglecting updates for outdated systems and failing to conduct regular safety audits to significantly enhance embedded software security and equipment protection.
