Introduction
In an era marked by the increasing interconnectivity of medical devices, the significance of embedded system cybersecurity is paramount. As healthcare technology advances, so too do the threats aimed at sensitive patient data and device functionality. This reality underscores the necessity for manufacturers to implement robust security measures.
This article examines best practices for bolstering cybersecurity in medical devices, highlighting essential strategies such as:
- Threat modeling
- Security-by-design principles
- Continuous monitoring
How can manufacturers ensure that their devices not only meet stringent regulatory standards but also remain resilient against the constantly evolving landscape of cyber threats?
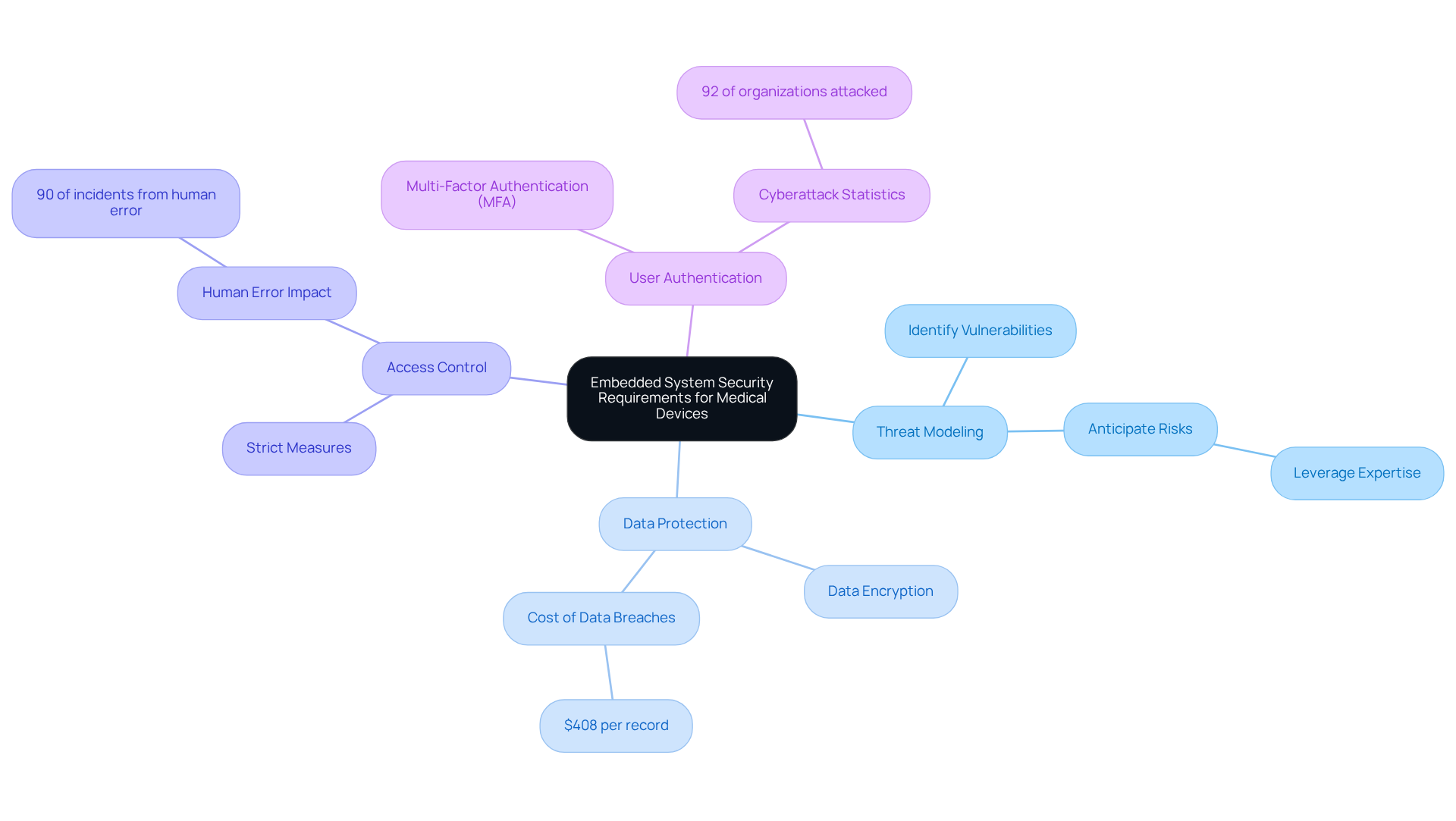
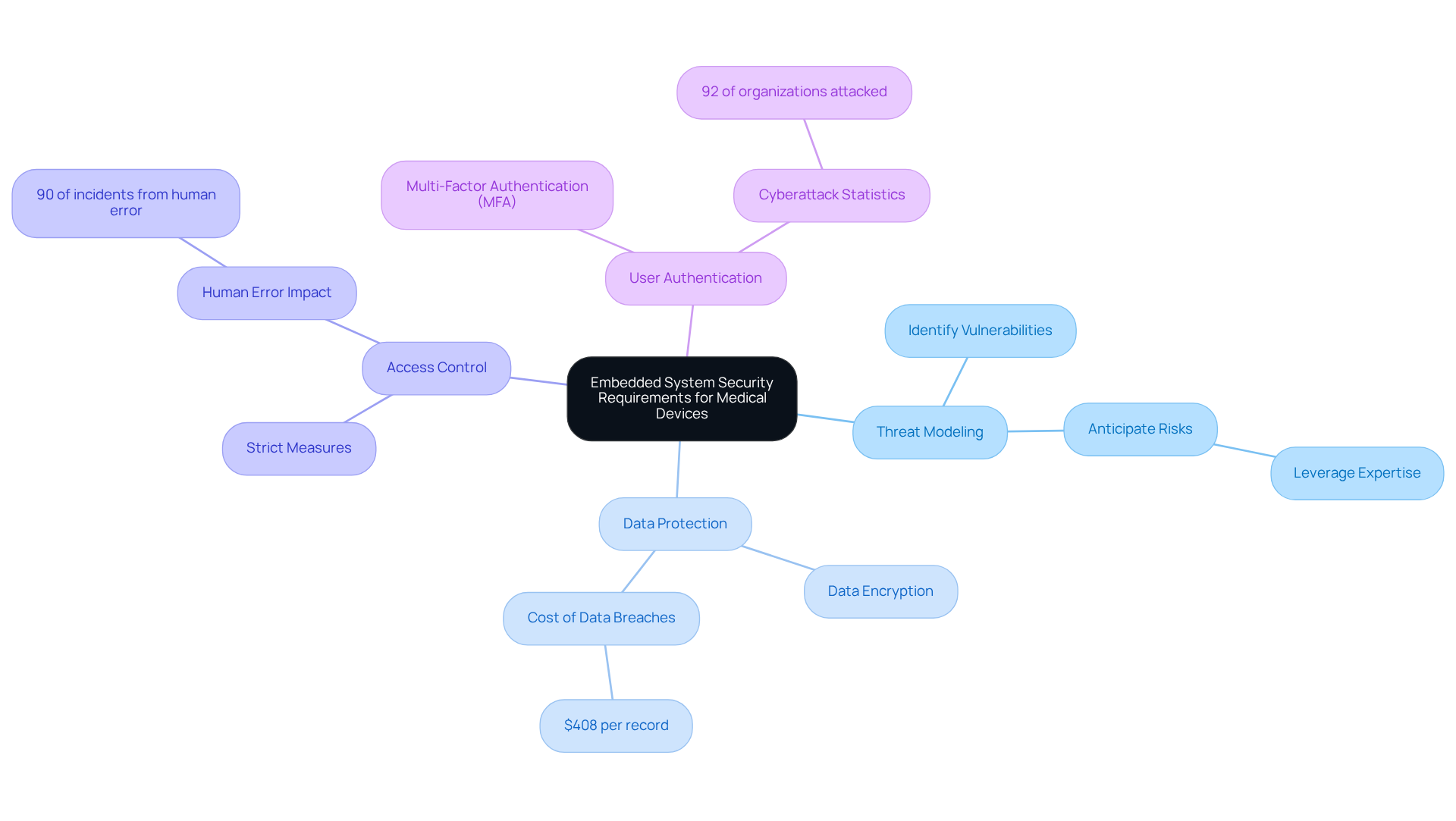
Understand Embedded System Security Requirements for Medical Devices
To effectively ensure in medical equipment, it is essential to understand the specific security requirements that govern their design and operation. This includes recognizing the unique challenges posed by connectivity, data privacy, and regulatory compliance. Key considerations are as follows:
- : Conducting a thorough exercise is crucial for identifying potential vulnerabilities and attack vectors specific to the device's functionality and connectivity. This proactive approach enables manufacturers, including Voler Systems, to anticipate and mitigate risks effectively by leveraging their expertise in compliant and reliable electronic product design.
- : Implementing robust data encryption methods is vital for safeguarding sensitive patient information, both at rest and in transit. With costing an average of $408 per record, ensuring data integrity is paramount to protect against significant financial and reputational damage.
- : Establishing strict measures ensures that only authorized personnel can access sensitive system components. This is essential in preventing unauthorized access, a significant factor in many healthcare data breaches. Given that , robust is critical in mitigating risks associated with human behavior.
- : Employing multi-factor authentication (MFA) enhances security for user access to the system, significantly reducing the risk of unauthorized entry. Recent statistics indicate that , underscoring the urgency of implementing strong authentication measures.
By addressing these requirements early in the design phase, manufacturers can create more secure products that not only meet user needs but also comply with stringent regulatory standards. The incorporation of best practices into the design process is crucial for developing robust healthcare instruments capable of withstanding evolving cyber threats, reflecting the importance of in Voler Systems' approach to .
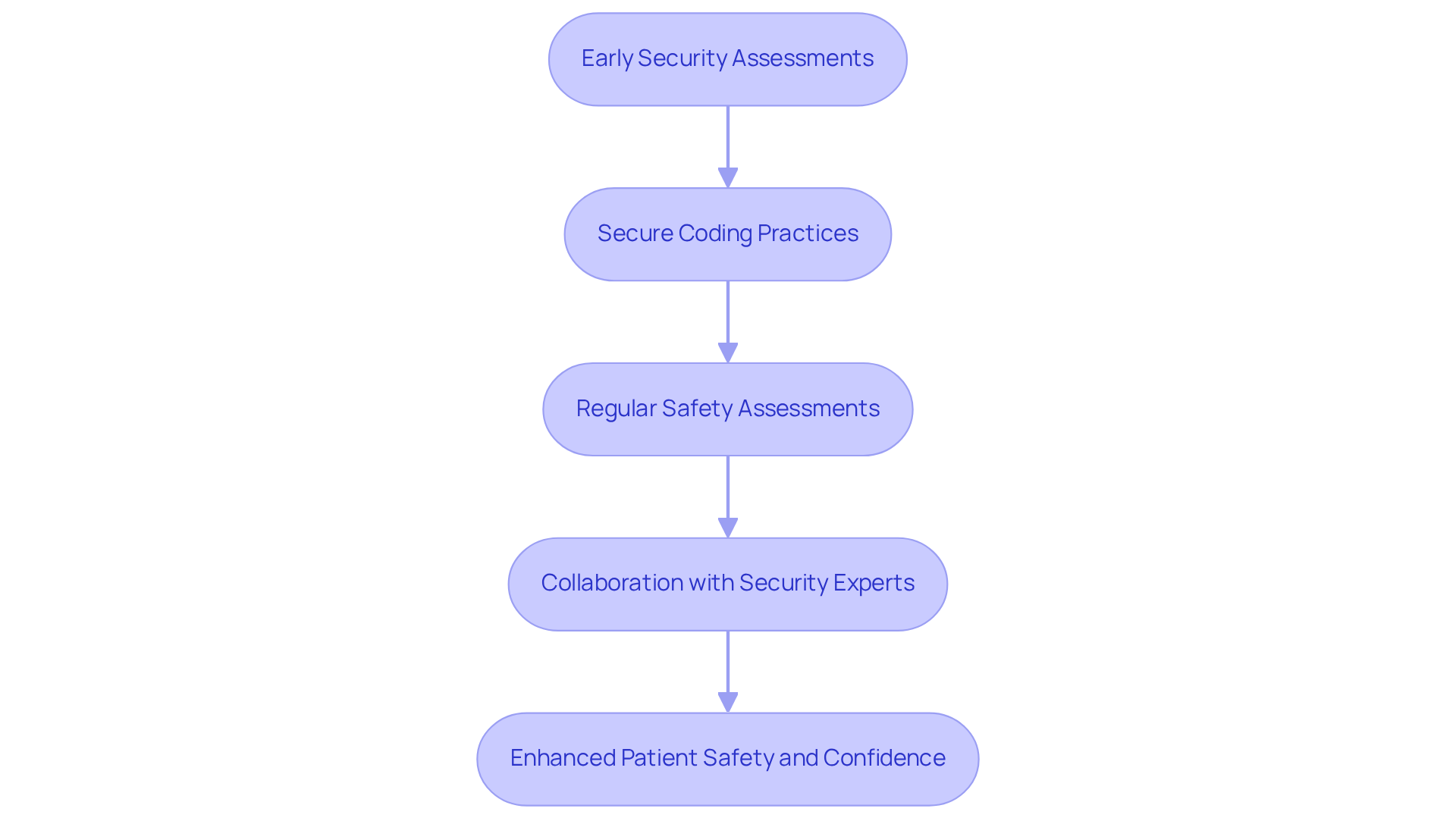
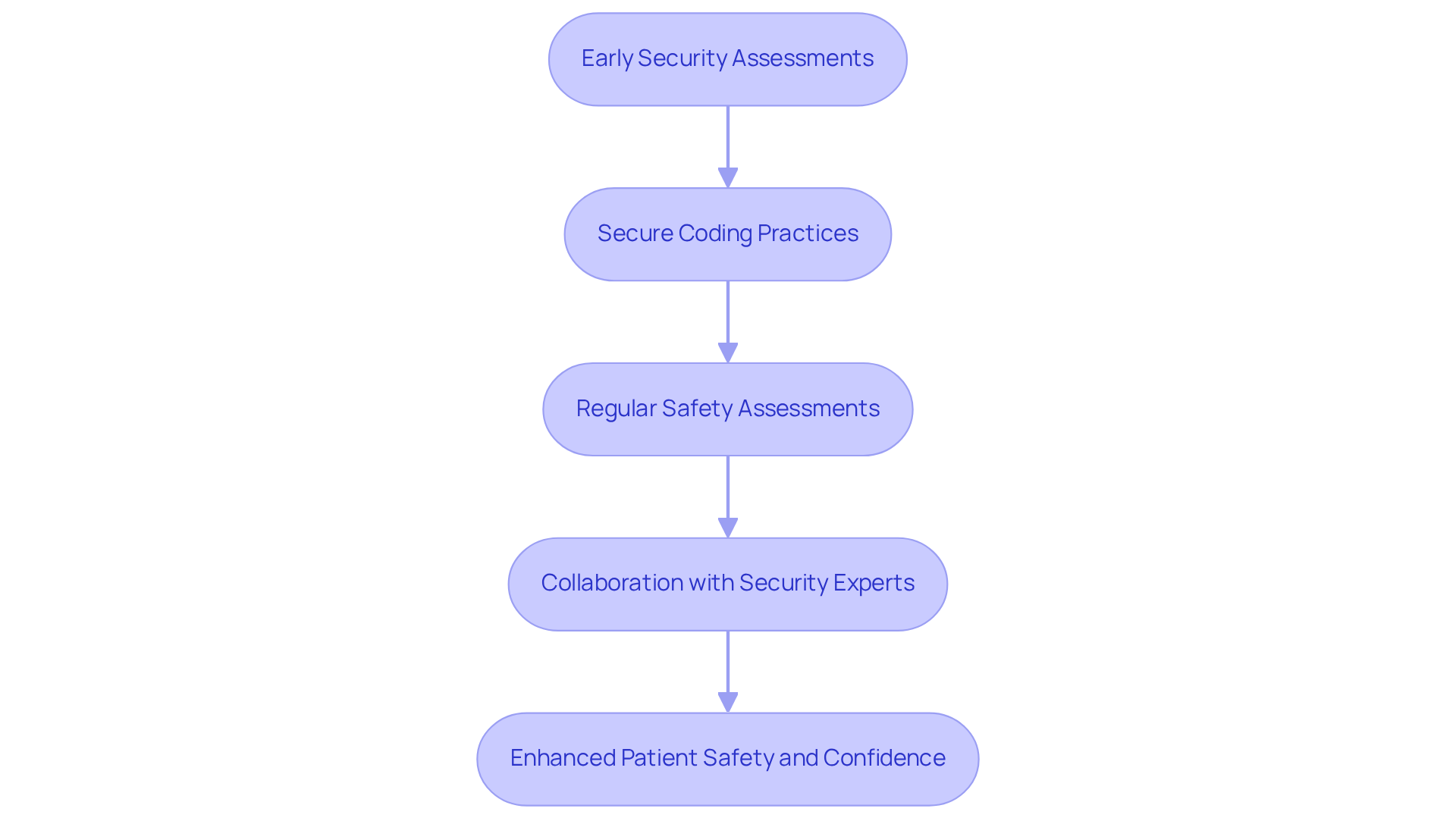
Implement Security-by-Design Principles in Development
Integrating security-by-design principles is essential for developing resilient . This ensures that are embedded throughout the entire . Key practices include:
- : Conducting security assessments during the initial design phase is crucial for identifying potential risks and vulnerabilities. Research indicates that only 14% of organizations feel fully prepared for emerging threats, highlighting the necessity for early intervention.
- : Training development teams on is vital to minimize the introduction of vulnerabilities during software development. A significant number of healthcare product manufacturers are adopting these practices, recognizing their importance in safeguarding patient information and maintaining equipment integrity.
- : Performing regular safety evaluations and audits throughout the development process ensures compliance with evolving safety standards. This continuous vigilance is critical, especially as global ransomware incidents surged by 32% in 2025, underscoring the increasing threats faced by interconnected healthcare devices.
- : Involving cybersecurity experts during the design phase offers valuable insights and recommendations on best practices. Their expertise can help manufacturers address vulnerabilities effectively and ensure that protection is a core aspect of product development.
By embedding protection into the design process, manufacturers can create products that are not only functional but also resilient against evolving cyber threats, ultimately enhancing patient safety and confidence in healthcare technology through .
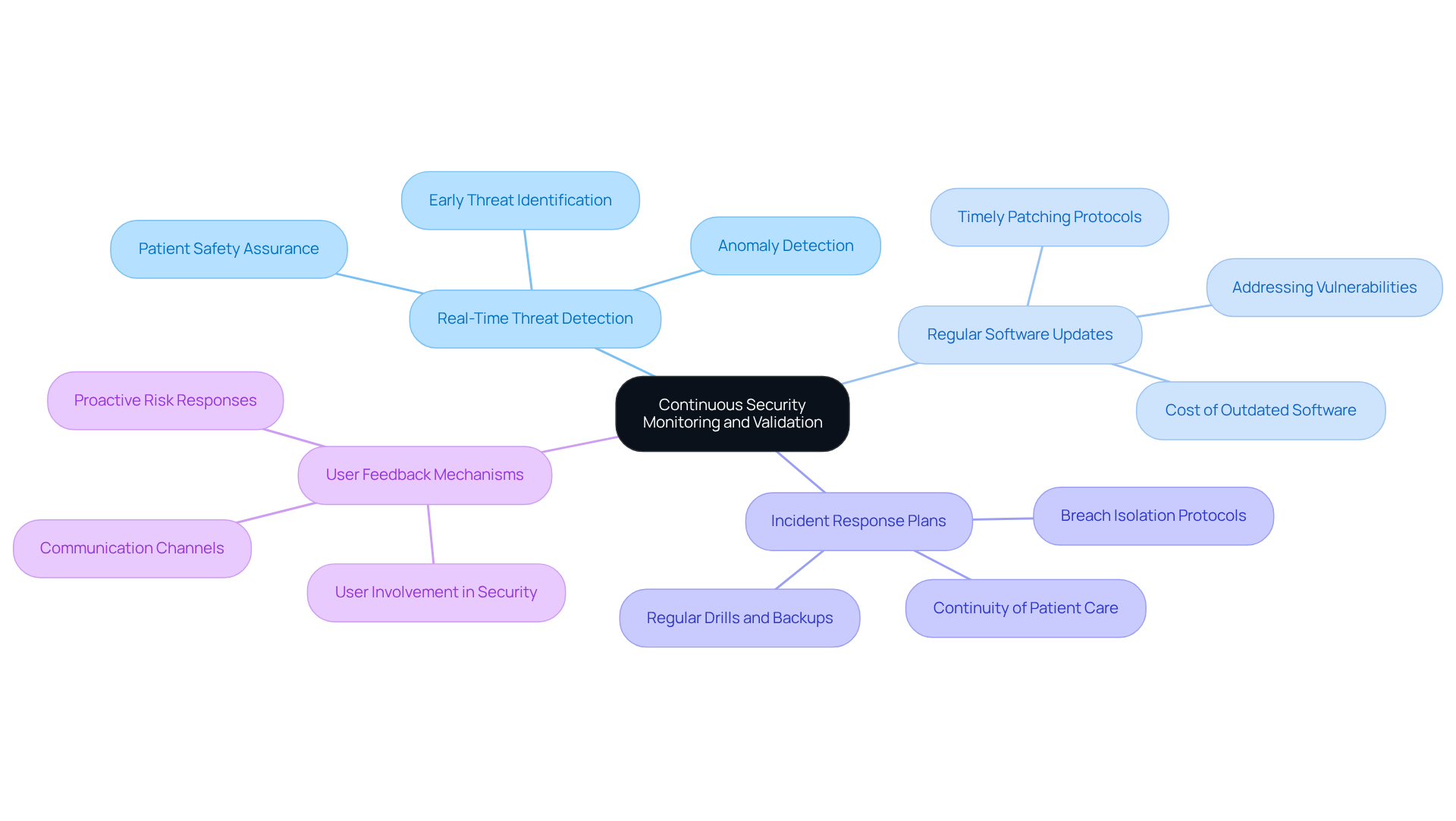
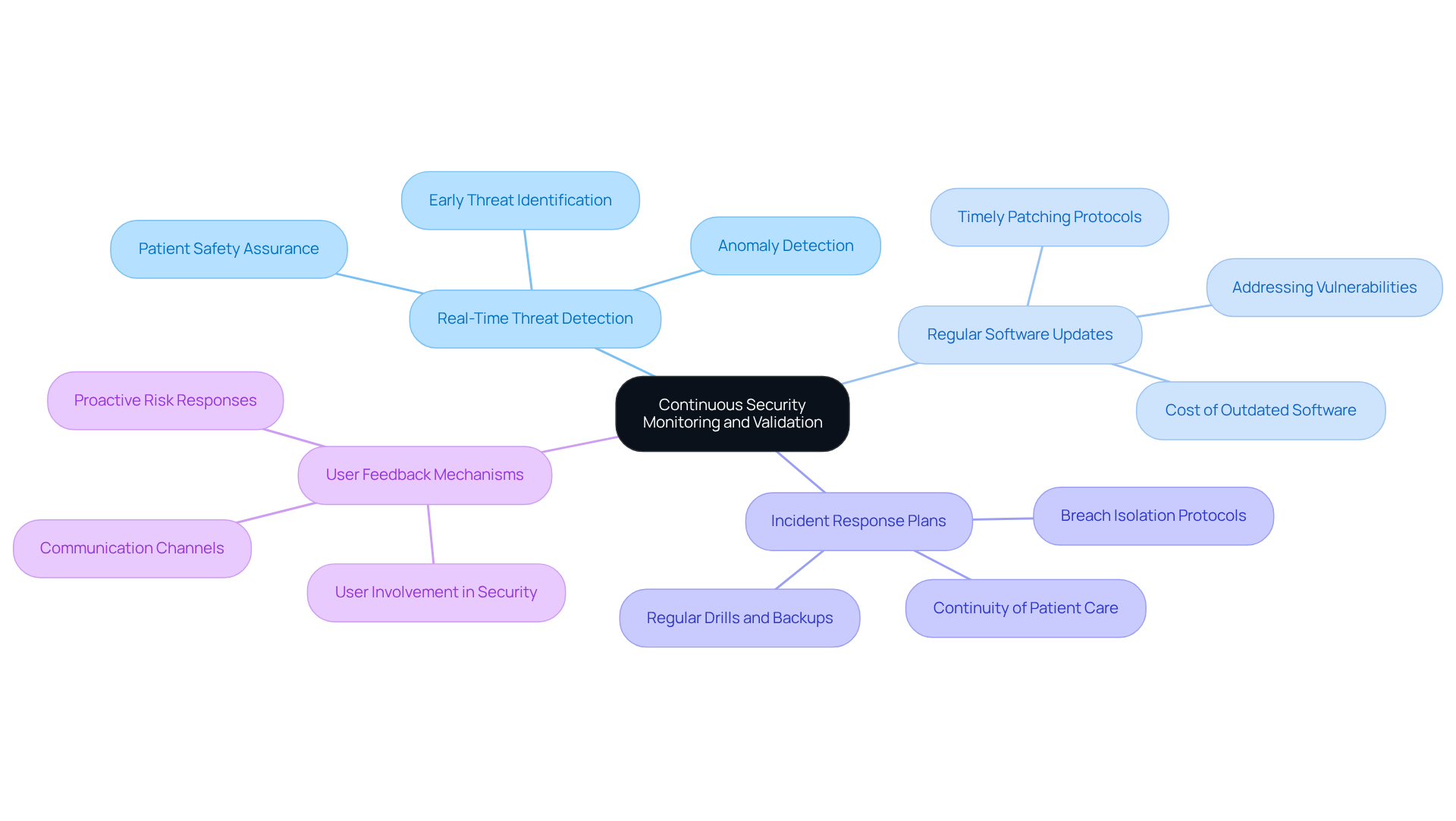
Maintain Continuous Security Monitoring and Validation
To ensure the ongoing protection of in medical equipment, it is essential to focus on through continuous monitoring and validation. This involves:
- Real-Time Threat Detection: Implement systems that provide to detect anomalies and potential security breaches. Such systems, utilizing embedded system , are vital as they can identify threats before they escalate, significantly reducing the risk of data breaches and ensuring patient safety.
- Regular : Establish a protocol for regular and patches to address . By 2026, should prioritize timely updates, as outdated software remains a primary target for cybercriminals. The has reached $10 million, highlighting the financial necessity of maintaining updated systems.
- : Develop and maintain to swiftly address any breaches that may occur. These plans should include protocols for isolating compromised equipment and ensuring that patient care continues safely during an incident.
- : Create channels for users to communicate concerns or irregularities, enabling proactive responses to potential risks. Involving users in the security process can enhance the overall security posture of healthcare equipment, as they often serve as the initial line of defense against emerging threats.
By maintaining constant observation and verification, manufacturers can quickly adapt to new risks and ensure the ongoing safety and efficacy of their healthcare products, particularly by addressing embedded system .
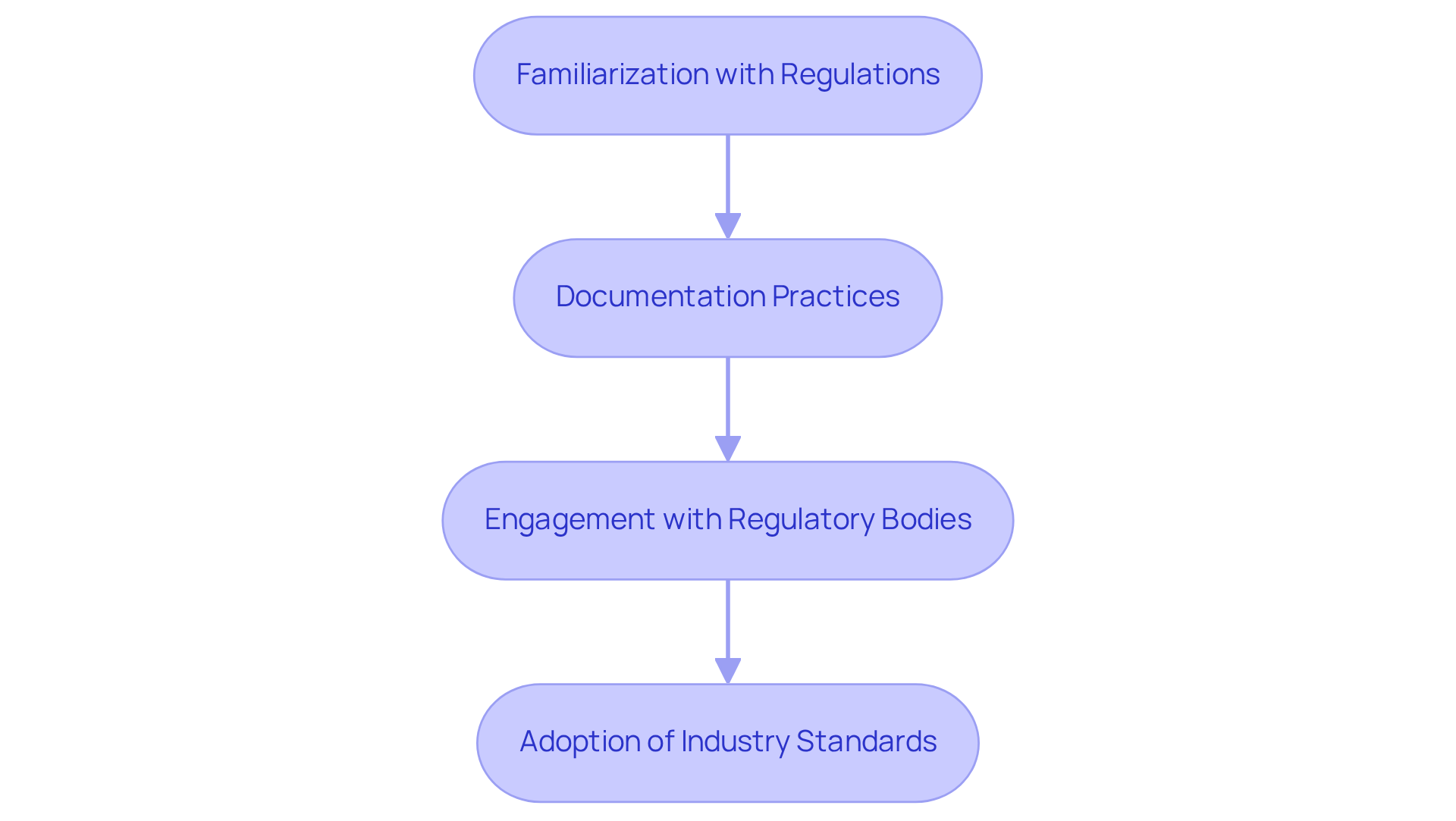
Ensure Compliance with Regulatory Standards and Best Practices
Adherence to is essential in the development of , particularly concerning . Key steps include:
- Familiarization with Regulations: Regularly update your knowledge of relevant regulations, including the , to ensure compliance throughout the device lifecycle. The FDA emphasizes that manufacturers must provide reasonable assurance of for their products, marking a shift from previous priorities focused solely on safety and effectiveness.
- Documentation Practices: Maintain comprehensive documentation of protective measures, risk assessments, and validation processes. This documentation is vital for demonstrating and must include a and a to effectively identify vulnerabilities. The FDA mandates that these documents be part of the eSTAR submission process to prevent refusal to accept decisions.
- Engagement with : Establish proactive communication with to clarify requirements and seek guidance on compliance strategies. This engagement aids in navigating the complexities of and ensures that all necessary documentation is in place.
- Adoption of Industry Standards: Adhere to established industry standards such as , which provide frameworks for managing safety and security risks in . The ANSI AAMI SW96 standard, recognized for its formal requirements, encourages manufacturers to integrate principles into their design controls and risk assessments.
By prioritizing compliance with these and best practices, manufacturers can enhance the credibility of their devices and facilitate smoother market entry.
Conclusion
Ensuring the cyber security of embedded systems in medical devices is not merely a technical necessity; it is a fundamental responsibility that manufacturers must embrace. By understanding specific security requirements, implementing security-by-design principles, maintaining continuous security monitoring, and ensuring compliance with regulatory standards, manufacturers can significantly enhance the resilience of their products against evolving cyber threats.
The article highlights several key practices essential for achieving robust embedded system cyber security. These include:
- Conducting thorough threat modeling
- Implementing strong data protection measures
- Establishing strict access controls
- Employing multi-factor authentication
Additionally, integrating security throughout the development lifecycle and maintaining vigilant monitoring are critical to safeguarding sensitive patient information and ensuring compliance with industry regulations.
As the landscape of cyber threats continues to evolve, it is imperative for manufacturers to adopt these best practices proactively. Emphasizing a culture of security within the development process not only protects patients but also fosters trust in healthcare technology. The commitment to embedded system cyber security must be unwavering, as it is integral to the integrity and safety of medical devices in today's interconnected healthcare environment.
Frequently Asked Questions
What are the key security requirements for embedded systems in medical devices?
The key security requirements include threat modeling, data protection, access control, and user authentication.
Why is threat modeling important in the design of medical devices?
Threat modeling is crucial for identifying potential vulnerabilities and attack vectors specific to the device's functionality and connectivity, allowing manufacturers to anticipate and mitigate risks effectively.
How can data protection be ensured in medical devices?
Robust data encryption methods should be implemented to safeguard sensitive patient information, both at rest and in transit, to protect against data breaches.
What role does access control play in medical device security?
Establishing strict access control measures ensures that only authorized personnel can access sensitive system components, which helps prevent unauthorized access and reduces the risk of healthcare data breaches.
What is the significance of user authentication in medical devices?
Employing multi-factor authentication (MFA) enhances security for user access, significantly reducing the risk of unauthorized entry, especially in light of the high incidence of cyberattacks in healthcare organizations.
How can manufacturers create more secure medical devices?
By addressing security requirements early in the design phase and incorporating threat modeling best practices, manufacturers can develop secure products that comply with regulatory standards and meet user needs.
List of Sources
- Understand Embedded System Security Requirements for Medical Devices
- 200 Inspirational Cybersecurity Quotes [2026] (https://digitaldefynd.com/IQ/inspirational-cybersecurity-quotes)
- cobalt.io (https://cobalt.io/blog/top-cybersecurity-statistics-for-2026)
- 80+ Healthcare Data Breach Statistics 2026 (https://getastra.com/blog/security-audit/healthcare-data-breach-statistics)
- varonis.com (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Implement Security-by-Design Principles in Development
- industrialcyber.co (https://industrialcyber.co/medical/hscc-previews-2026-ai-cybersecurity-guidance-highlighting-best-practices-for-healthcare-organizations)
- 200 Inspirational Cybersecurity Quotes [2026] (https://digitaldefynd.com/IQ/inspirational-cybersecurity-quotes)
- Secure by Design: A Crucial Imperative for Medical Device Teams (https://jamasoftware.com/blog/secure-by-design-a-crucial-imperative-for-medical-device-teams)
- varonis.com (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- Navigating the FDA's Cybersecurity Guidance for Medical Devices (https://blog.securityinnovation.com/navigating-the-fdas-cybersecurity-guidance-for-medical-devices)
- Maintain Continuous Security Monitoring and Validation
- Key Healthcare Cybersecurity Stats to Know for 2024 (https://asimily.com/blog/healthcare-cybersecurity-key-statistics-2024)
- IoMT Vulnerabilities Statistics 2025: Record Exposure in Healthcare (https://deepstrike.io/blog/iomt-vulnerabilities-statistics-2025)
- 2026 Healthcare Cybersecurity Trends: What IT Leaders Need to Know Now (https://meriplex.com/2026-healthcare-cybersecurity-trends-what-it-leaders-should-expect-next-year)
- Security vulnerabilities in healthcare: an analysis of medical devices and software - PMC (https://pmc.ncbi.nlm.nih.gov/articles/PMC10758361)
- Ensure Compliance with Regulatory Standards and Best Practices
- censinet.com (https://censinet.com/perspectives/fda-medical-device-vendor-compliance-third-party-risk-management-best-practices)
- FDA Releases Final Guidance on Medical Device Cybersecurity (https://emergobyul.com/news/fda-releases-final-guidance-medical-device-cybersecurity)